Enabling Secure Remote Access: A Comprehensive Guide to G Network Setup for Remote Access VPN
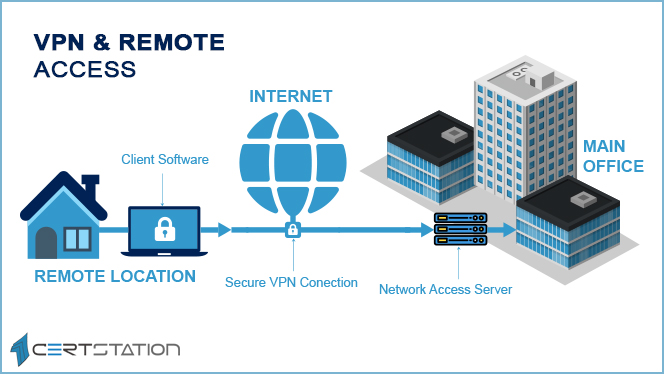
In today's interconnected world, remote access has become an essential aspect of modern business. With the proliferation of cloud computing, mobile devices, and the increasing number of remote workers, securing remote access has become a top priority for organizations. In this guide, we will explore the concept of G Network Setup for Remote Access VPN and provide a comprehensive overview of the essential steps to enable secure remote access.What is Remote Access VPN?
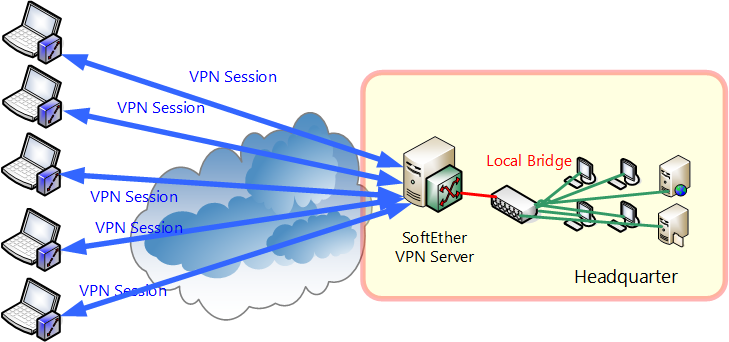
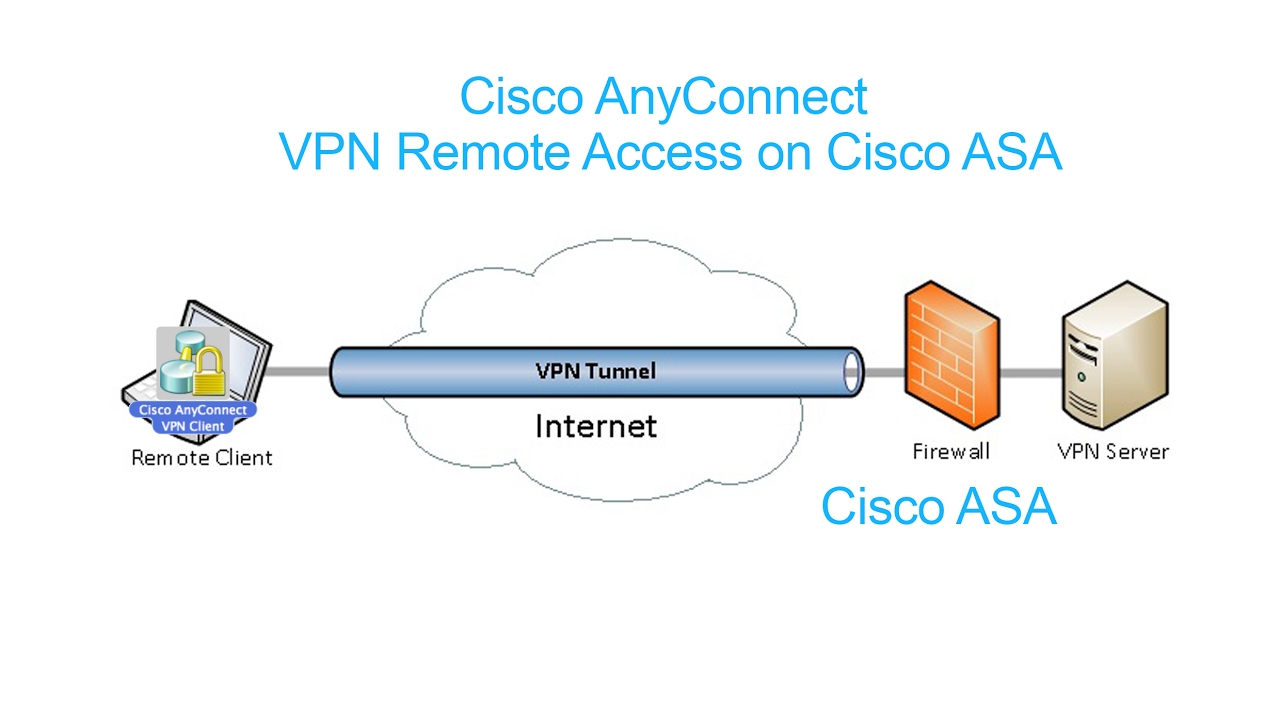
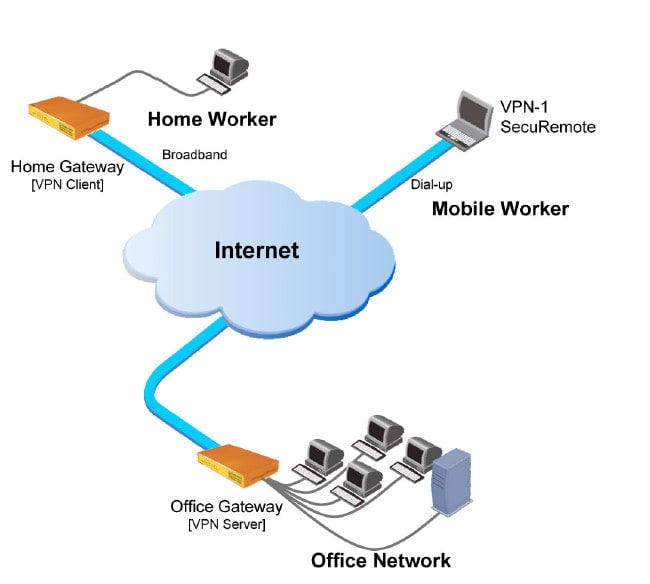
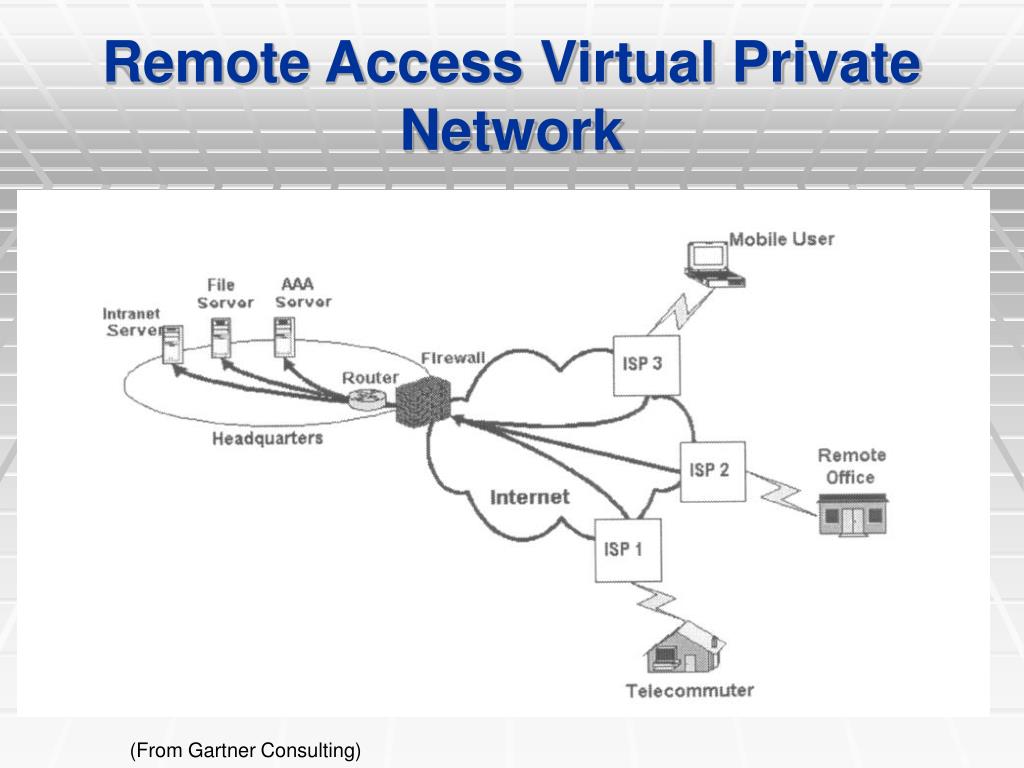
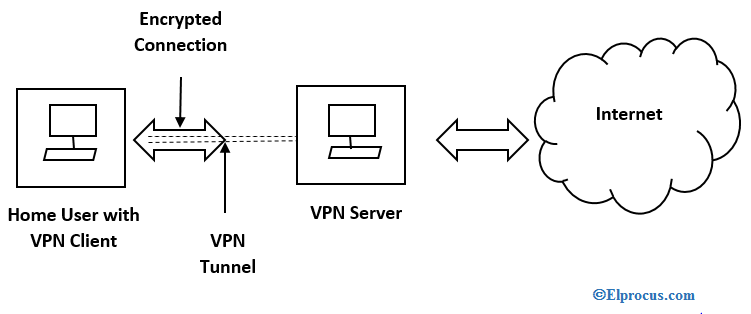
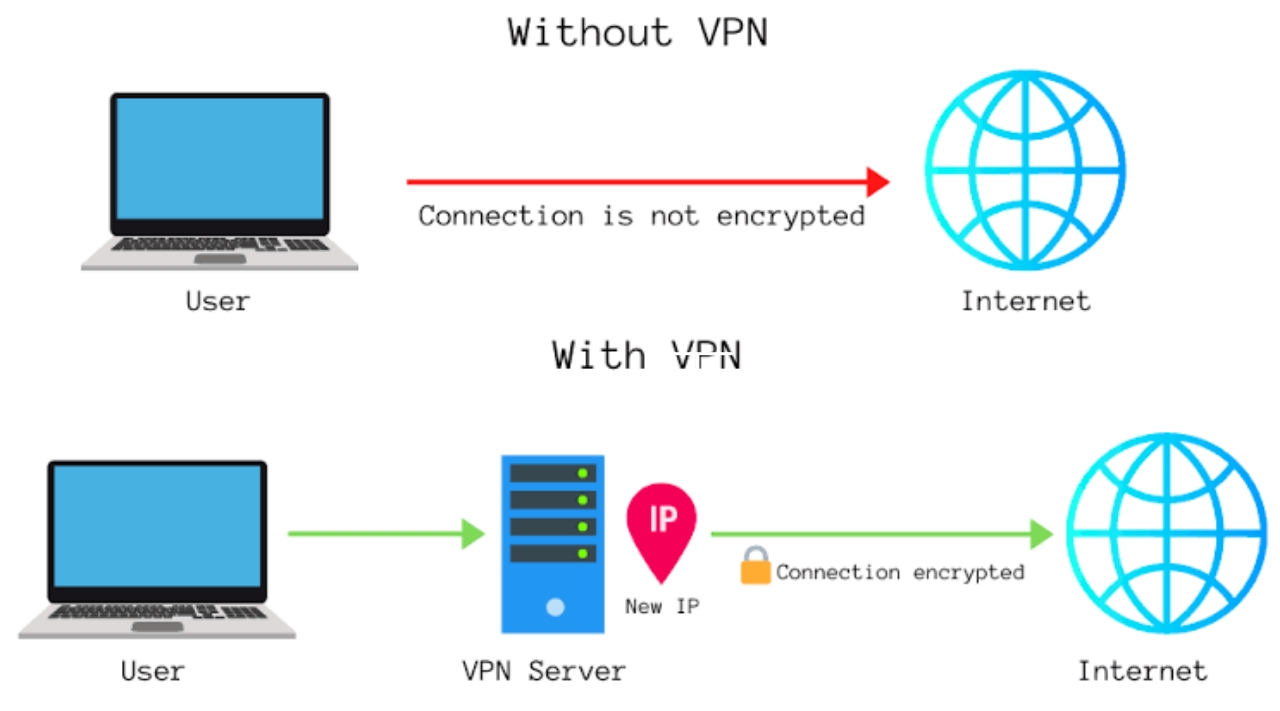
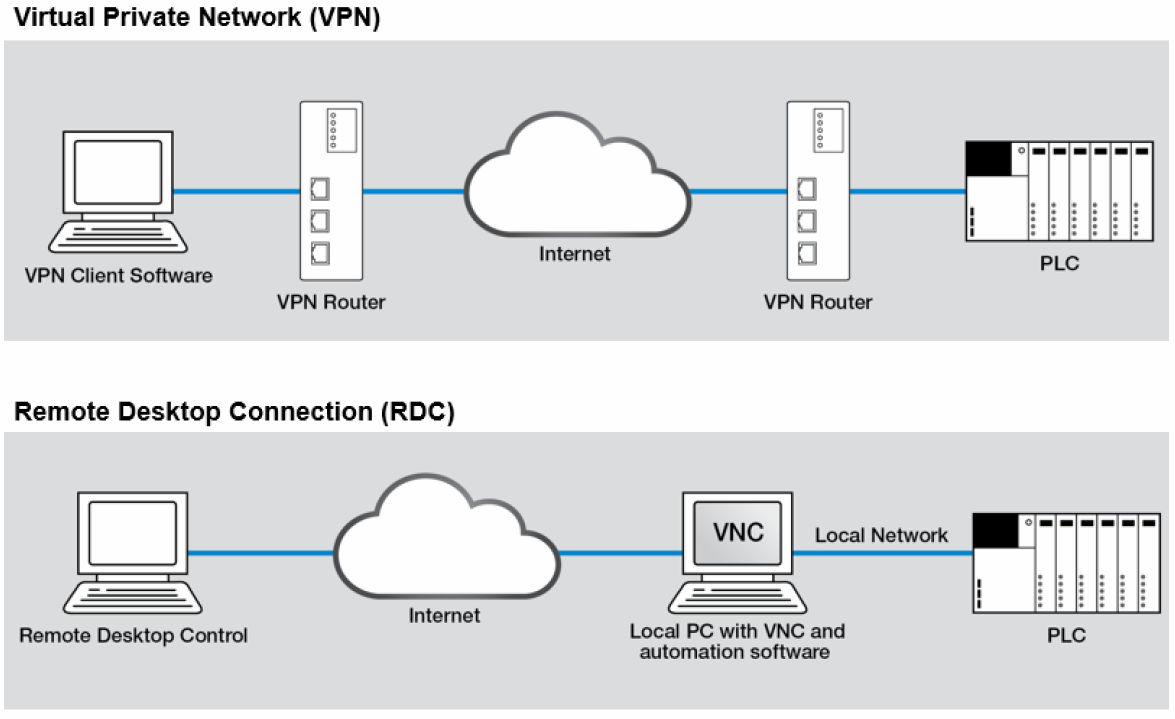
A Remote Access VPN (Virtual Private Network) is a technology that allows users to securely access a private network over the internet. This is achieved by creating a secure tunnel between the user's device and the private network, using encryption and tunneling protocols. The primary purpose of a Remote Access VPN is to provide secure and encrypted access to a private network, allowing users to work remotely while maintaining the security and integrity of the network.Benefits of G Network Setup for Remote Access VPN

Types of Remote Access VPNs
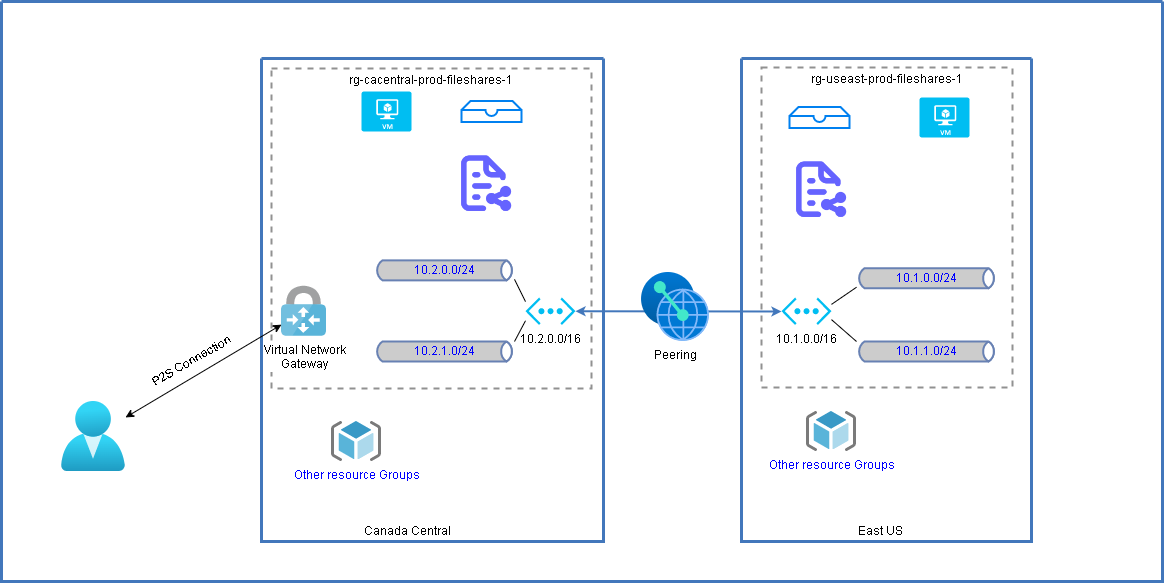
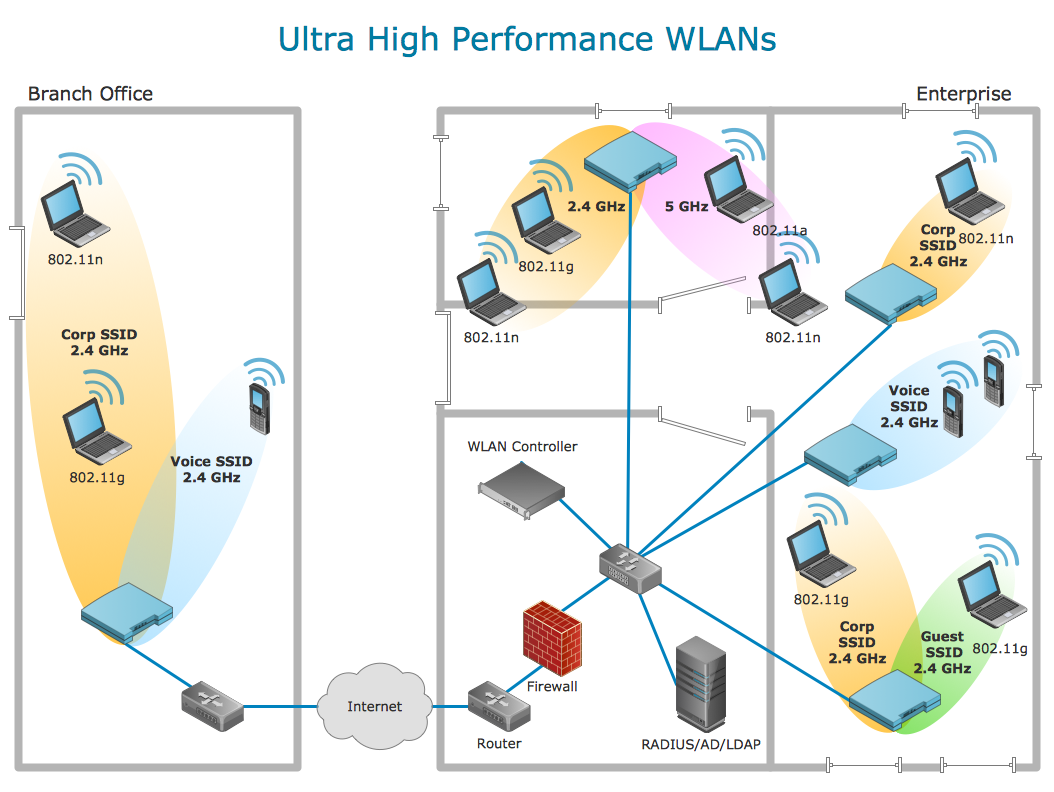
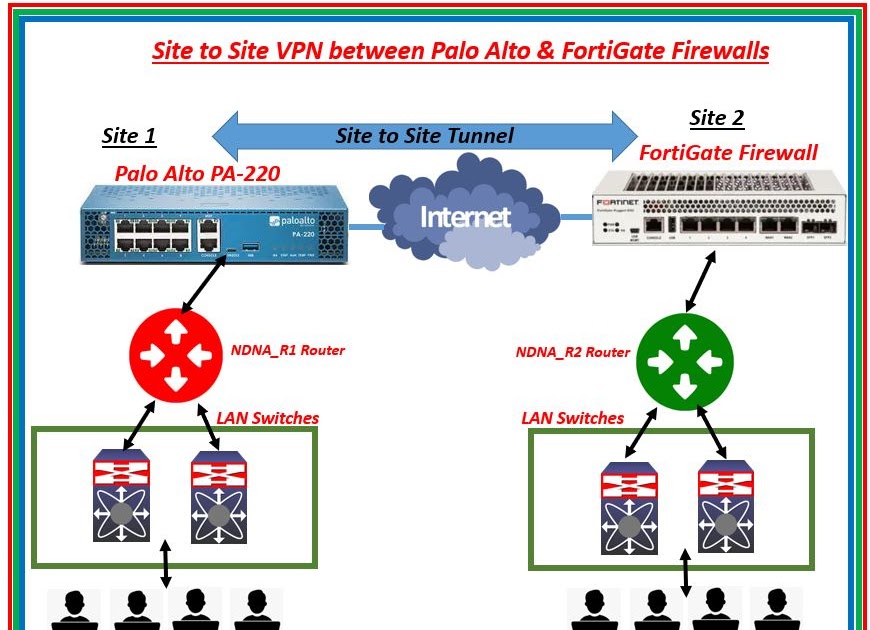
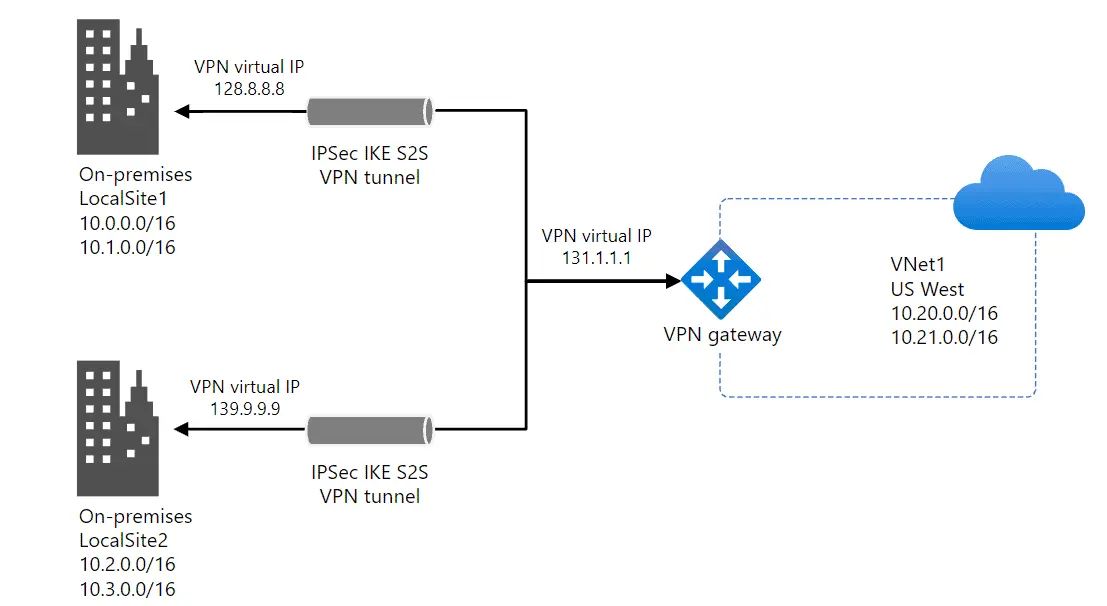
There are two primary types of Remote Access VPNs: * **Client-Server VPN**: In this architecture, a client connects to a VPN server, which provides secure access to the private network. * **Site-to-Site VPN**: In this architecture, two or more networks are connected through a VPN, allowing users to access resources on the connected networks.Requirements for G Network Setup for Remote Access VPN

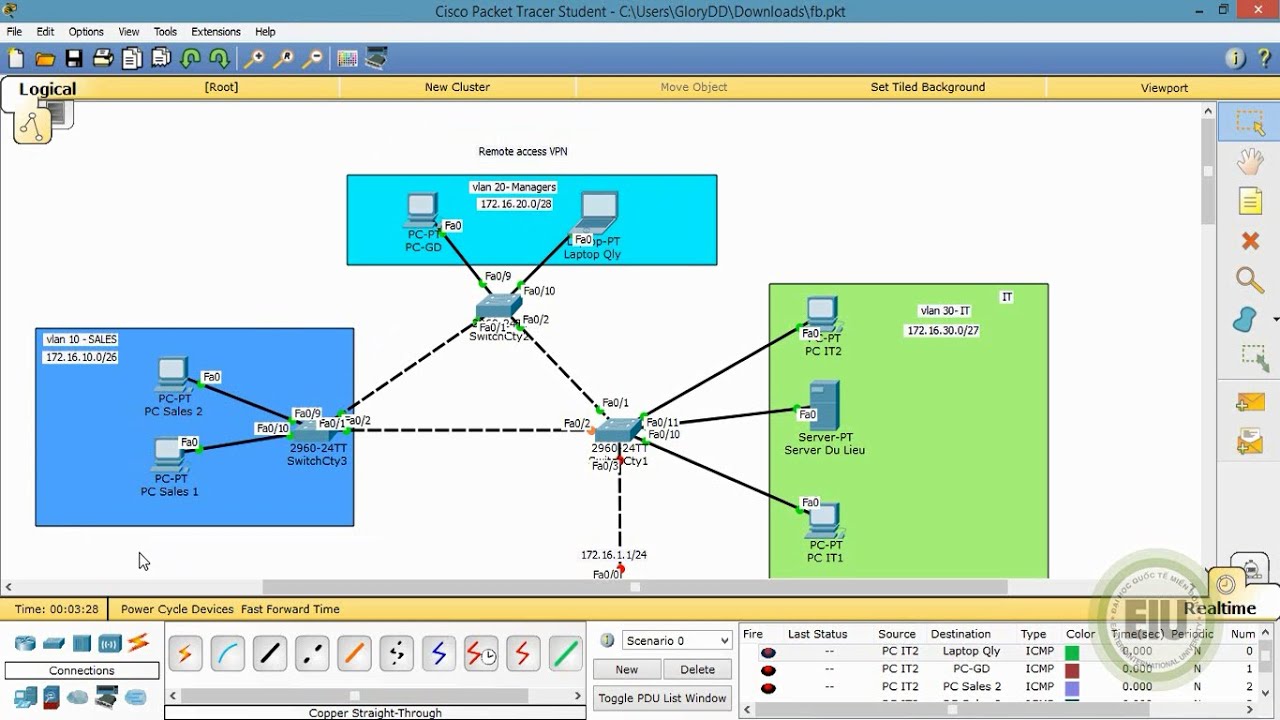
Step-by-Step Guide to G Network Setup for Remote Access VPN
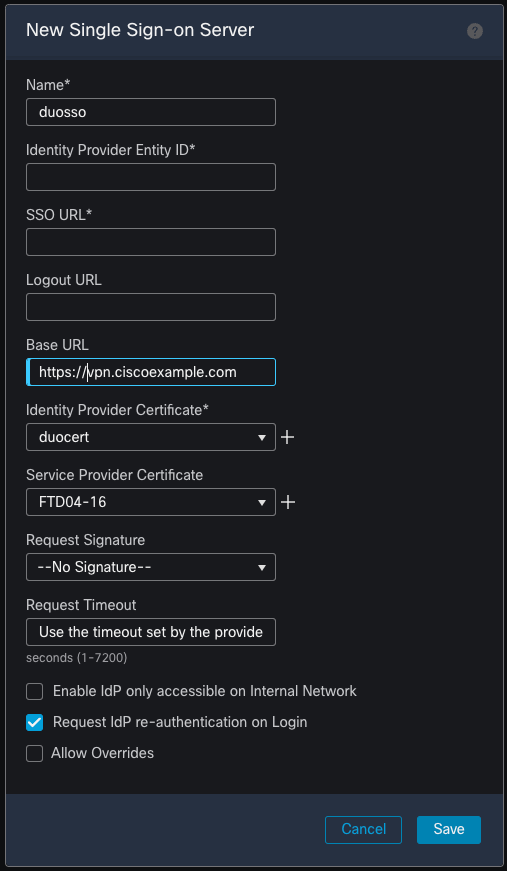
The following step-by-step guide provides a comprehensive overview of the essential steps to enable secure remote access: 1. **Configure the Network Infrastructure**: Set up a stable and reliable network infrastructure that supports VPN connectivity. 2. **Configure Firewalls**: Configure firewalls to allow VPN traffic. 3. **Implement Authentication and Authorization**: Implement authentication and authorization mechanisms to ensure that only authorized users can access the private network. 4. **Install VPN Software**: Install suitable VPN software on the client device. 5. ** Configure VPN Settings**: Configure VPN settings, including username, password, and server address. 6. **Test VPN Connectivity**: Test VPN connectivity to ensure that the setup is working correctly.Best Practices for G Network Setup for Remote Access VPN

Moving forward, it's essential to keep these visual contexts in mind when discussing G Network Setup For Remote Access Vpn.
To ensure the security and integrity of the private network, the following best practices must be observed: * **Regularly Update and Patch VPN Software**: Regularly update and patch VPN software to ensure that security vulnerabilities are addressed. * **Use Strong Passwords and Authentication Mechanisms**: Use strong passwords and authentication mechanisms to ensure that only authorized users can access the private network. * **Implement Encryption**: Implement encryption to ensure that data transmitted between the user's device and the private network remains confidential and secure. * **Monitor VPN Traffic**: Monitor VPN traffic to detect and prevent any unauthorized access or malicious activity.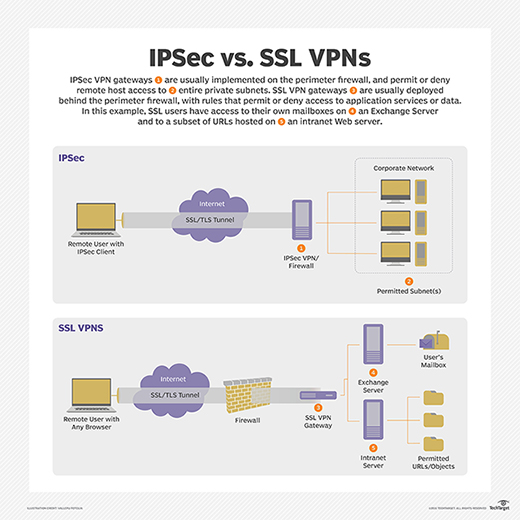








![Install Pritunl VPN on Rocky Linux / AlmaLinux [Guide] Install Pritunl VPN on Rocky Linux / AlmaLinux [Guide]](https://image.slidesharecdn.com/networkaccessprotectionppt-140818230425-phpapp02/85/Network-access-protection-ppt-8-320.jpg)