G Wireless Network Security Configuration for Finance: Protecting Your Business from Wireless Threats
Overview of Wireless Network Security Configuration for Finance


Implementing a securewirelessnetwork: Businesses rely heavily onwirelessnetworksto ensure seamless communication, enhance productivity, and keep up with the fast-paced demands of the market. However, aswirelessnetworksbecome more integral to business operations, the need for enhancednetworksecurityhas never been more important. Cybercriminals often target unsecurednetworks, which ...

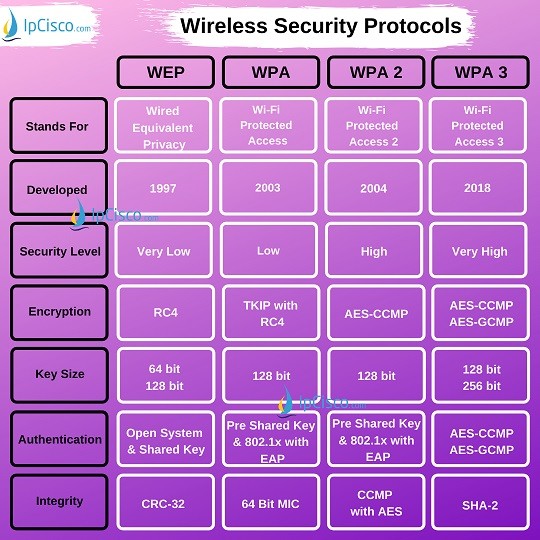
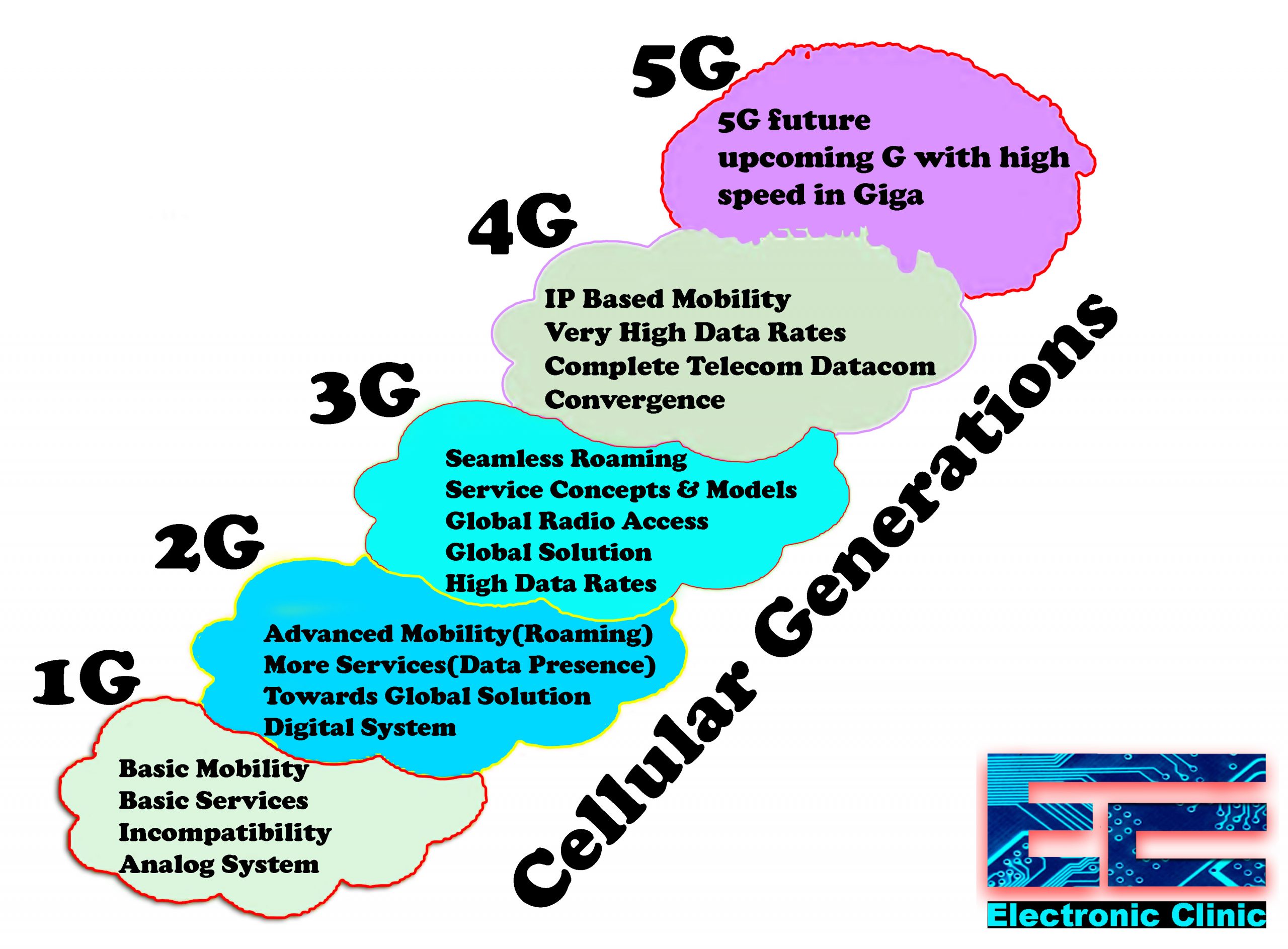
This comprehensive guide will discusswirelessnetworksecurity, from the basics of WEP and WPA to advanced concepts like cloudsecuritybest practices.

Jun 5, 2025What isWirelessNetworkSecurity?Wirelessnetworksecurityrefers to the strategies, technologies, and protocols used to protect data as it travels overwirelessnetworks. Without propersecurityin place, your business becomes an easy target for cybercriminals looking to exploit vulnerabilities in yournetwork.

Linksys WUSB54GS. This comprehensive guide covers everything from planning yourwirelessnetworkto troubleshooting common issues with a USBnetworkadapter. Learn to connect and monitor yournetworkeffectively.
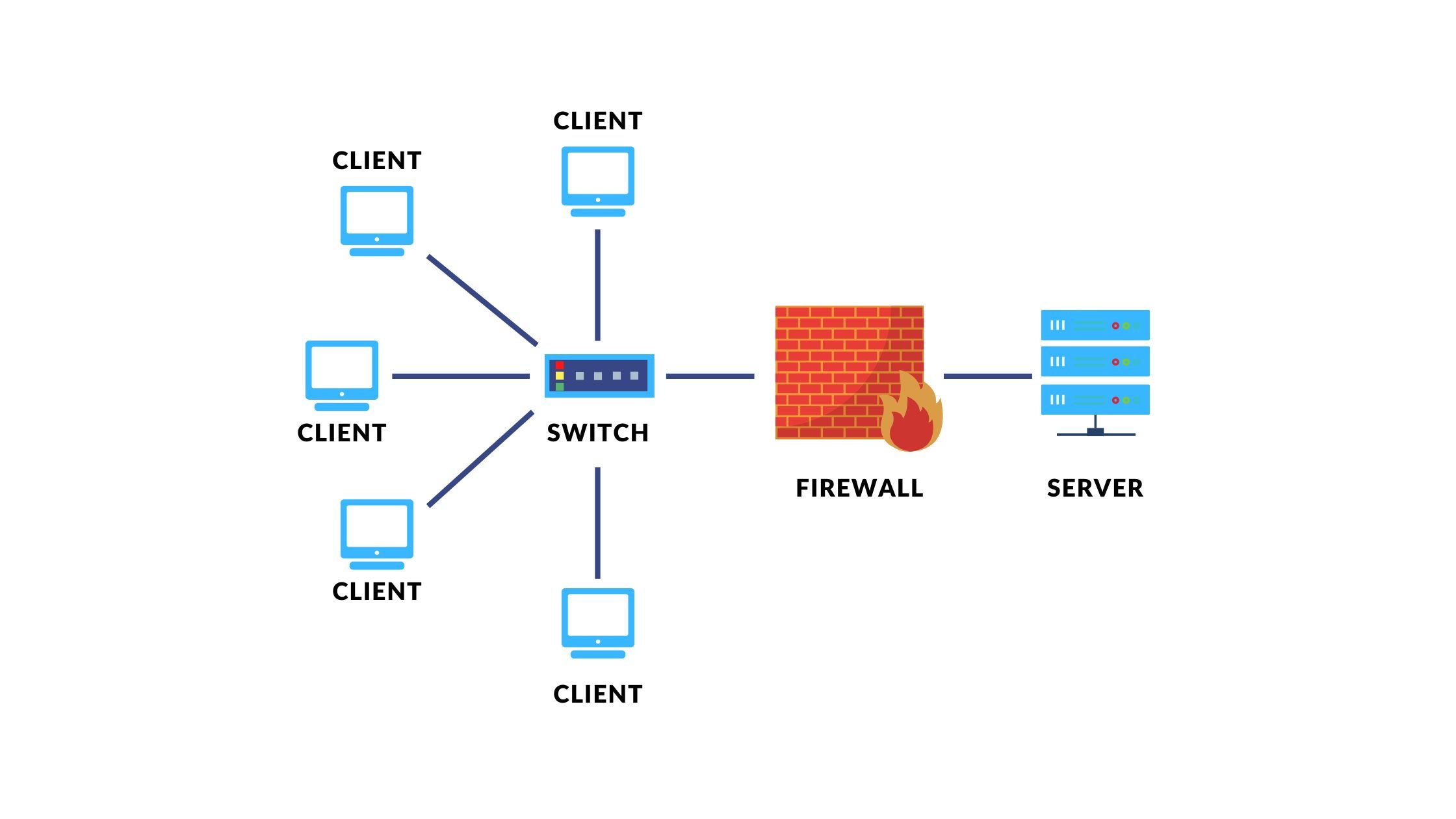
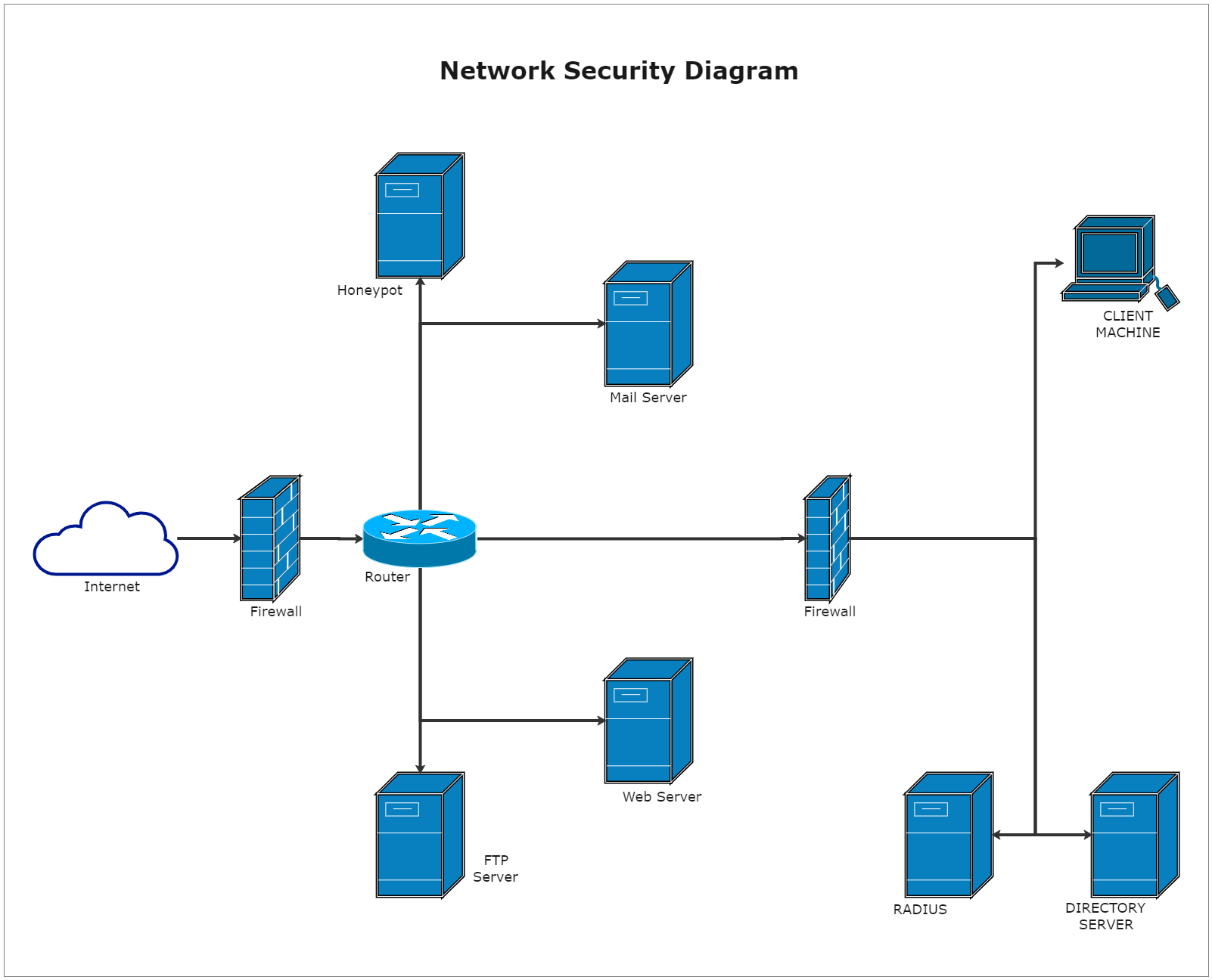
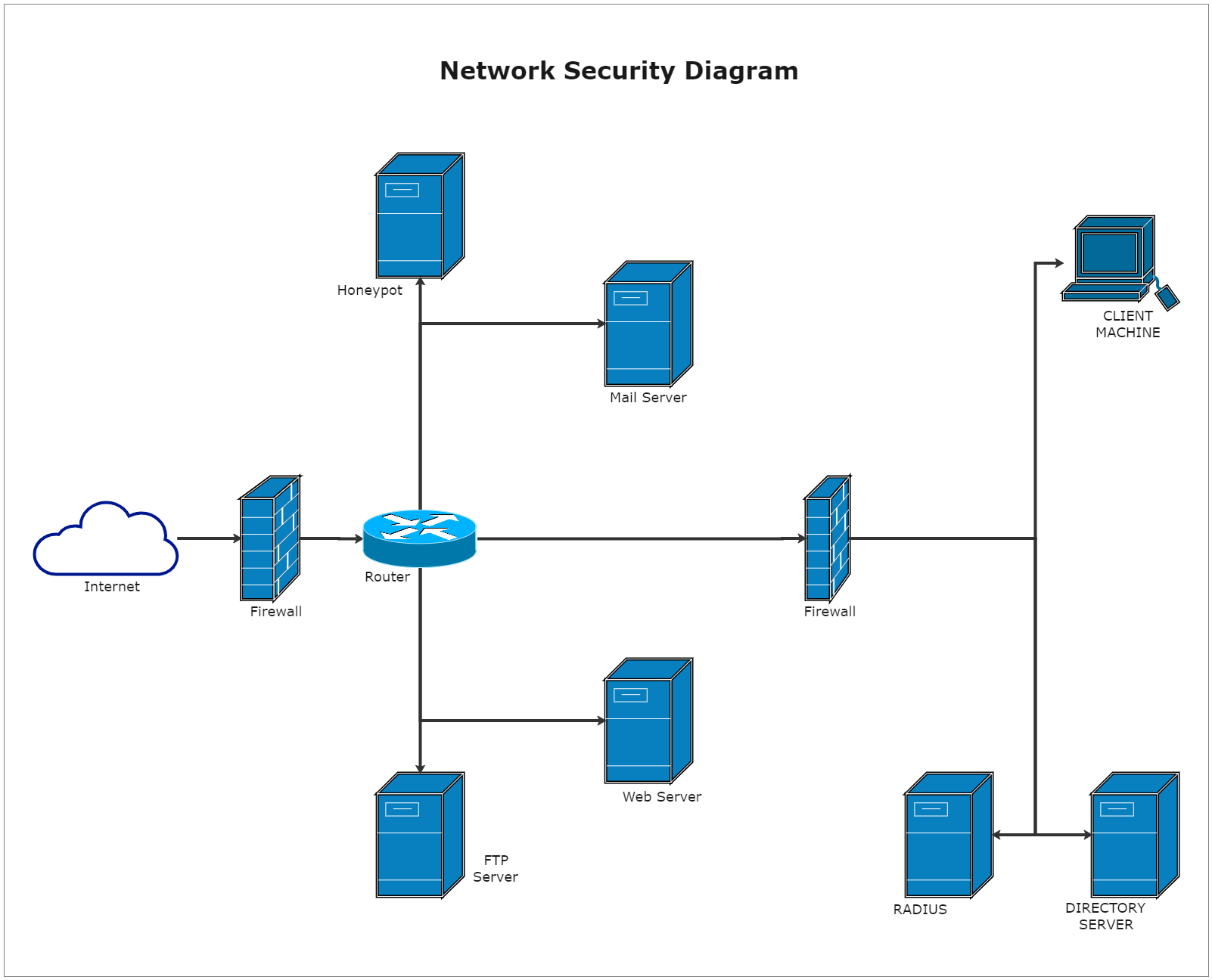
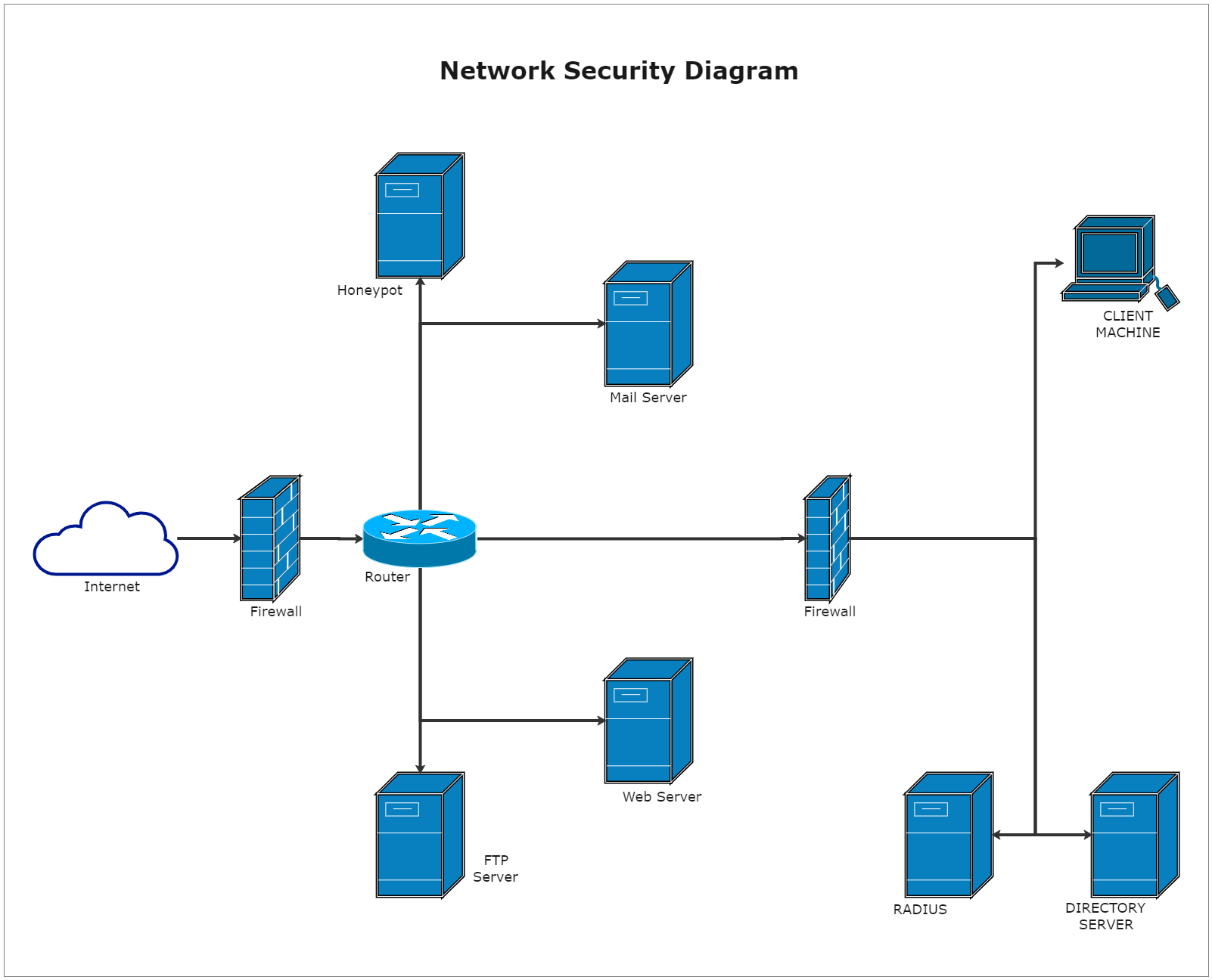
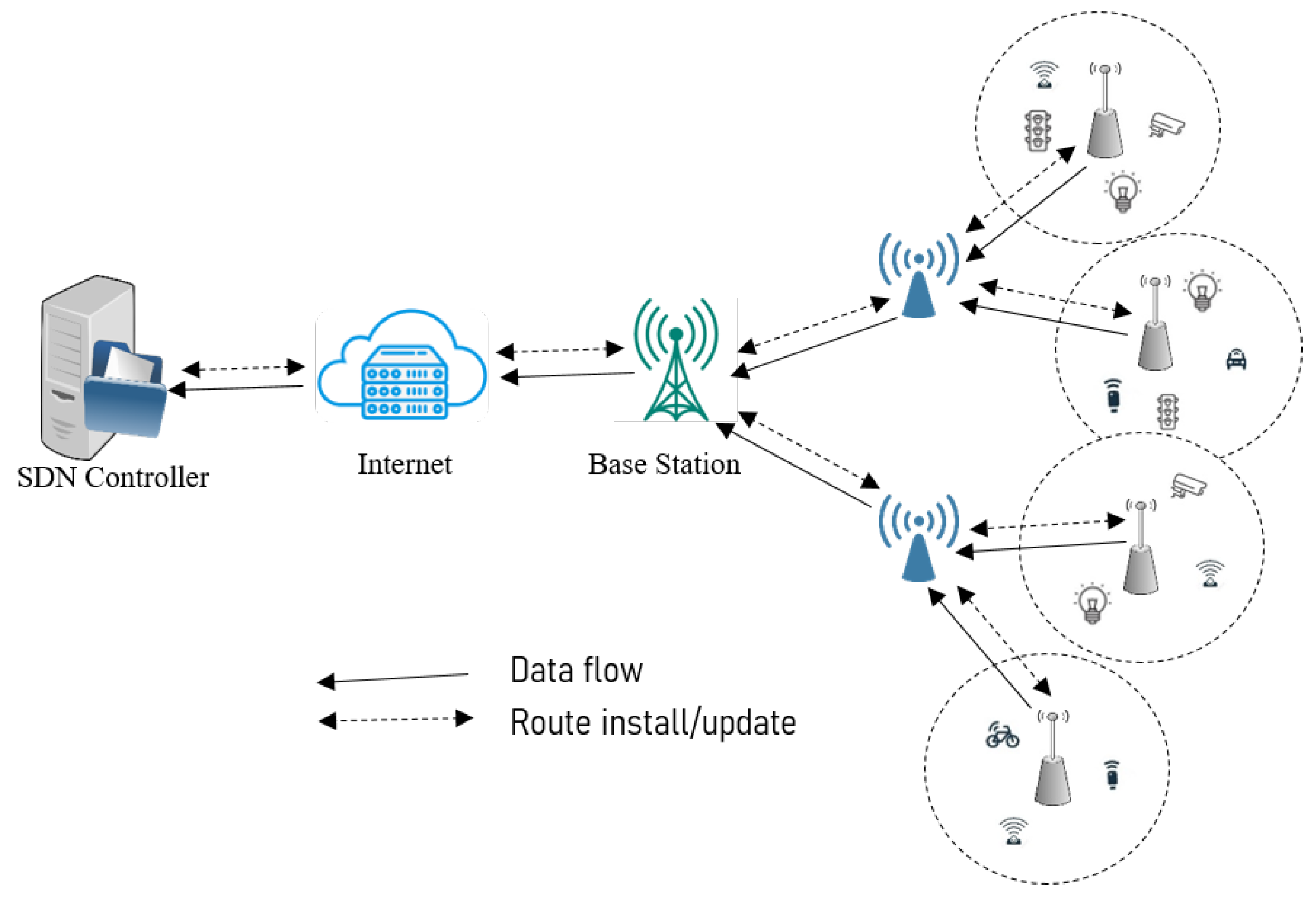
What is enterprisenetworksecurity? Enterprisenetworksecurityis the protection of anetworkthat connects systems, mainframes, and devices―like smartphones and tablets―within an enterprise. Companies, universities, governments, and other entities use enterprisenetworksto connect their users to information and people. Asnetworksgrow in size and complexity,securityconcerns increase.
Learn the best practices for securing yourwirelessnetworkin a bank, credit union, or other financial service provider. Find out how to encrypt, configure, protect, and monitor yournetworkand ...

Derex Technologies is currently looking for a ArubaWirelessLevel 3NetworkEngineer near Boston. Full job description and instant apply on Lensa.

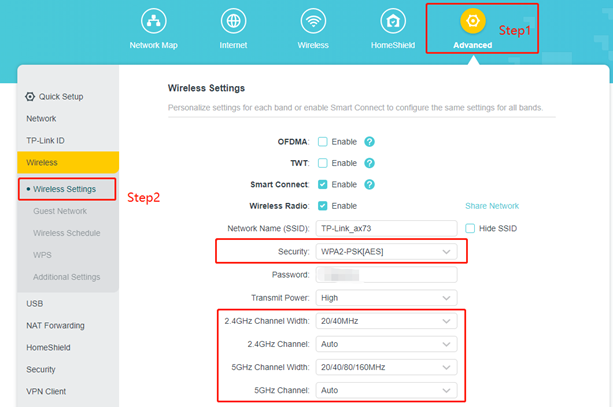
This document explains the advantages of the use of Wi-Fi Protected Access 2 (WPA 2) in aWirelessLAN (WLAN). The document provides twoconfigurationexamples on how to implement WPA 2 on a WLAN. The first example shows how to configure WPA 2 in enterprise mode, and the second example configures WPA 2 in personal mode.

Informationsecurityis the process by which a financial institution protects the creation, collection, storage, use, transmission, and disposal of sensitive information, including the protection of hardware and infrastructure used to store and transmit such information. Informationsecuritypromotes the commonly accepted objectives of confidentiality, integrity, and availability of ...

Jan 14, 2026ConfigurationWorkflow The WPA3configurationworkflow consists of two main steps: Create a WLAN using WPA3-Enterprise, WPA3-Personal, or OWE (OpportunisticWirelessEncryption). (Optional) Enable SSIDs for Wi-Fi 7, if thenetworkincludes Wi-Fi 7 access points. This step is required due to the additionalsecurityrequirements introduced with ...
These "unmanaged" sites can act as a conduit for threats to the corporate network—laptops risk contracting viruses, spyware, and malware.Wirelessclients can exacerbate the problem by connecting towirelessaccess points or otherwirelessclients without the user's knowledge.

Jul 2, 2025Whether you're asecurityanalyst or a small business owner, yourwirelessconfigurationcan make or break your overallsecurityposture. How Enterprise Wi-FiSecurityWorks Enterprisewirelesssecurityis all about layered protection.
1. Introduction This guide summarizes leading practices and technical guidance for securingnetworksfromwirelessthreats and for securely implementingwirelessaccess tonetworks. This document is specifically focused on thewirelesstechnologies commonly referred to as "Wi-Fi" as defined in the Institute of Electrical and Electronics Engineers (IEEE) 802.11 family. This guide does not ...
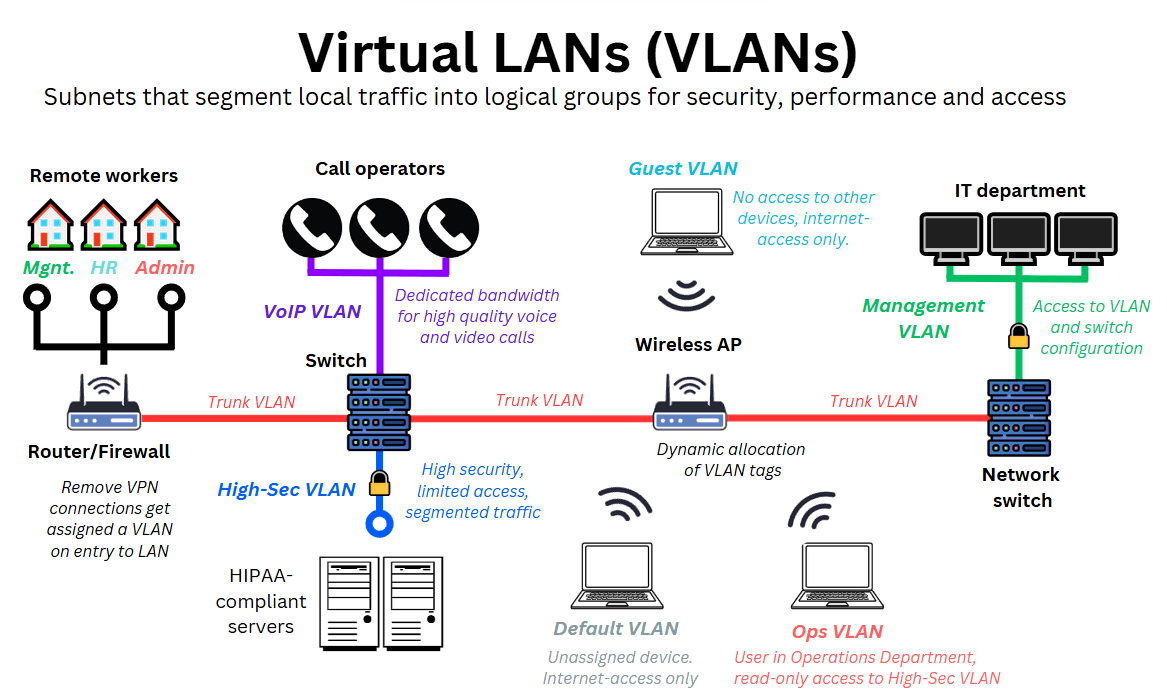
1.1. Document purpose and Scope This Information Supplement provides guidance and recommendations for deployingwirelessnetworksincluding 802.11 Wi-Fi and 802.15 Bluetooth technologies, in accordance with the Payment Card Industry DataSecurityStandard (PCI DSS). The goal is to help organizations understand and interpret how PCI DSS applies towirelessenvironments, how to limit the PCI DSS ...

WIFISECURITYCONFIGURATIONBEST PRACTICES Solid Wi-Fisecurityconfigurationsare essential for protecting company data, preventing unauthorized access, and complying with cybersecurity best practices.

These 12 best practices are essential for securing yourwirelessnetworkand ensuring that your data and devices are safe from malicious actors.

Learn how to configure and securewirelessnetworks, including setting up SSIDs, encryption, and managingwirelessclients.

How to implementwirelessnetworksecurityinto enterprise Wi-Fi design? Check our project-based article to get the tips you need.

Learn about modems and Internet connections,security, sharing files and printers, and how to set up awirelessnetworkin your home.
Black Box is a global leader in digital infrastructure solutions, deliveringnetworkand system integration, managed services, and technology products to Fortune 100 and top global enterprises. With a presence across the United States, Europe, India, Asia Pacific, the Middle East, and Latin America, Black Box serves businesses across financial services, technology, healthcare, retail, public ...

Sep 15, 2025Wirelesssecurityis critically important for protectingwirelessnetworksand services from unwanted attacks. Here's a quick guide to follow.
Dec 18, 2024PCI DSS Requirement 1.2.2: Managenetworkchanges through change control (fornetworksecurity) This requirement emphasizes the importance of managing changes tonetworkconnections andconfigurationsof NSCs through a formal change control process defined in Requirement 6.5.1 (implement a change control process). This ensures that allnetworkmodifications are reviewed, approved, documented ...

Propernetworksegmentation significantly reduces the ability for an adversary to reach and exploit these other systems (see Cybersecurity and InfrastructureSecurityAgency's (CISA's) "LayeringNetworkSecurityThrough Segmentation" and NSA's "SegmentNetworksand Deploy Application-aware Defenses") [1], [2].
Securityoperations (28%) Computing resources: applying secure baselines, mobile solutions, hardening,wirelesssecurity, applicationsecurity, sandboxing, and monitoring. Asset management: explaining acquisition, disposal, assignment, and monitoring/tracking of hardware, software, and data assets.
:max_bytes(150000):strip_icc()/001_connecting-android-device-to-wifi-577618-755697d5bc5649c9aa05c973cc6e76ae-00e87780bf824c61b6872ec93285bdbe.jpg)
We would like to show you a description here but the site won't allow us.
Verify the encryption of yournetworkwith NetSpot and choose the bestwirelesssecurityprotocol to secure your WiFi. Get more information about possiblesecurityprotocols: WEP, WPA, WPA2, and WPA3.
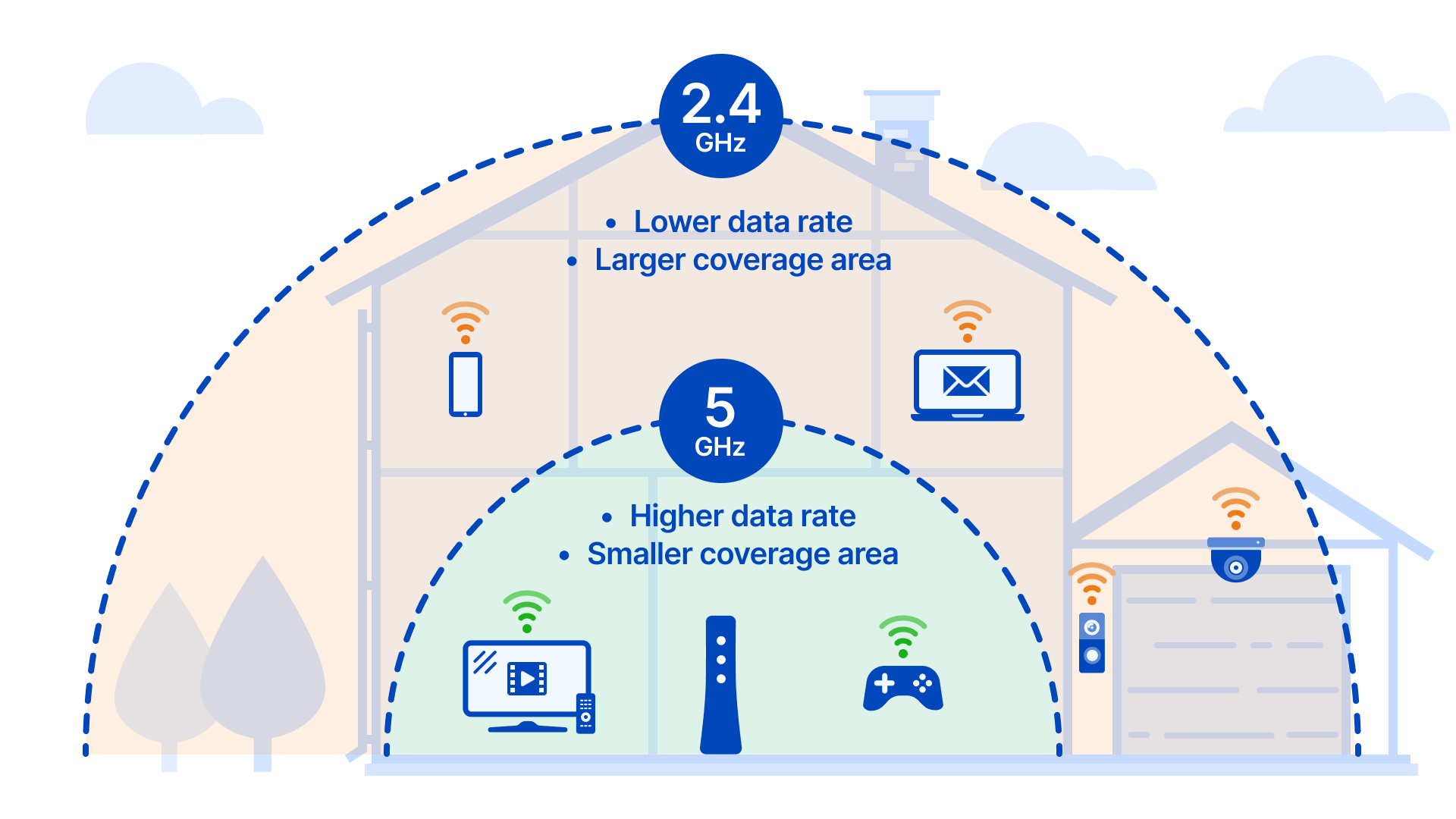
Wi-Fisecurityis the protection of devices andnetworksconnected in awirelessenvironment. Without Wi-Fisecurity, a networking device such as awirelessaccess point or a router can be accessed by anyone using a computer or mobile device within range of the router'swirelesssignal.

Learn the top threats facingwirelessLANs, the evolution of WLANsecurityprotocols andwirelessnetworkbest practices to keep your organization safe.
Overview of the PCI DSSWirelessGuideline Information Supplement The near ubiquity ofwirelessnetworksmakes them a top priority for organizations that store, process or transmit cardholder data. In response, the PCISecurityStandards Council Special Interest Group Implementation Team has published an information supplement called PCI DSSWirelessGuideline.

Business WiFisecuritycan be improved by applying basic practices and cybersecurity tools to keep company data safe onwirelessnetworks.