Protecting against Malware in Cryptocurrency Transactions: Essential Strategies for Crypto Security
As the world of cryptocurrency continues to grow, so do the threats to digital asset security. With the rise of cryptocurrency transactions, the risk of malware attacks has increased exponentially. In this comprehensive guide, we will delve into the world of cryptocurrency security, exploring the most effective strategies to protect against malware in cryptocurrency transactions.Awareness is Key: Understanding Malware and Its Impact on Cryptocurrency
Malware, or malicious software, is designed to compromise computer systems and steal sensitive information. In the context of cryptocurrency transactions, malware can be particularly devastating, as it can manipulate transactions, theft funds, and disrupt services. The cryptocurrency ecosystem is particularly vulnerable to malware, as transactions are irreversible and most data-stealing malware is designed to function silently in the background.Urgent Steps to Protect Your Digital Wallet: Tips and Strategies
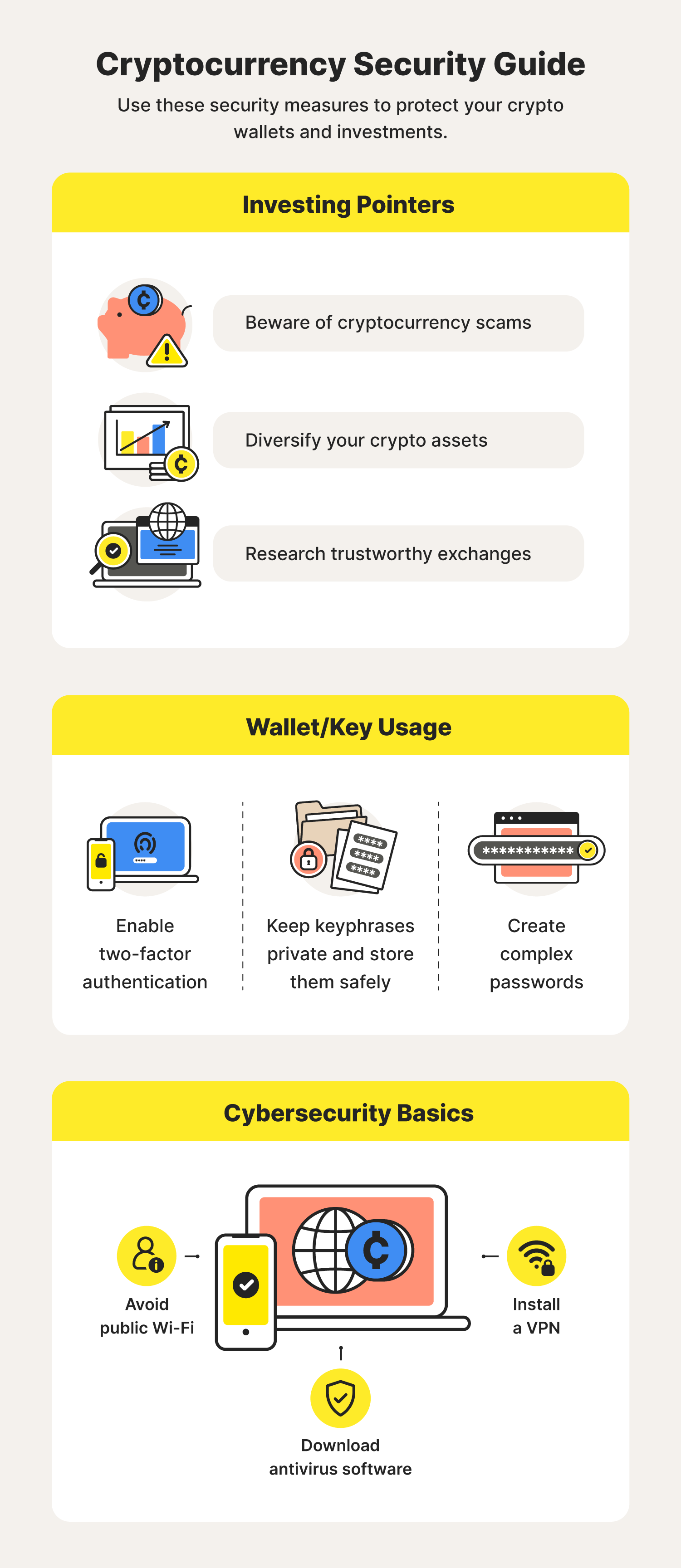
To safeguard against malware in cryptocurrency transactions, it is essential to implement a multi-layered approach to security. Here are some urgent steps to protect your digital wallet: *Use AntiVirus Software:
AntiVirus software is a crucial tool in the fight against malware. Award-winning software like TotalAV offers real-time protection against threats, removing stealthy malware like RATs and Keyloggers. Ensure you have the latest software and regularly update your antivirus programs. *Verify the Authenticity of Apps and Plugins:
Use a Separate Device for Crypto Transactions:
Consider using a dedicated device for cryptocurrency transactions. This will help prevent accidental installations of malware and reduce the risk of sensitive information compromise. *Monitor Accounts and Funds Regularly:
Stay vigilant and regularly monitor your accounts and funds to detect any suspicious activity. Track transactions using tools like Etherscan or Blockchain Explorer to ensure the integrity of your cryptocurrency transactions.Protecting Against Advanced Malware Threats: A Comprehensive Guide
In addition to the above strategies, consider the following advanced security measures to protect against malware in cryptocurrency transactions: *Use a Beefy Firewall:

Enable Two-Factor Authentication (2FA):
Activate 2FA to add an additional layer of security, making it more challenging for hackers to gain access to your cryptocurrency wallet. *Keep Software Up-to-Date:
Regularly update your device's operating system and application software to ensure you have the latest security patches and features. *Use Secure Online Storage:
Consider using secure online storage solutions like encrypted cloud storage to protect sensitive information.Real-World Examples of Malware Attacks on Cryptocurrency Transactions