Protecting against Malware on IoT Devices: A Comprehensive Guide
Introduction
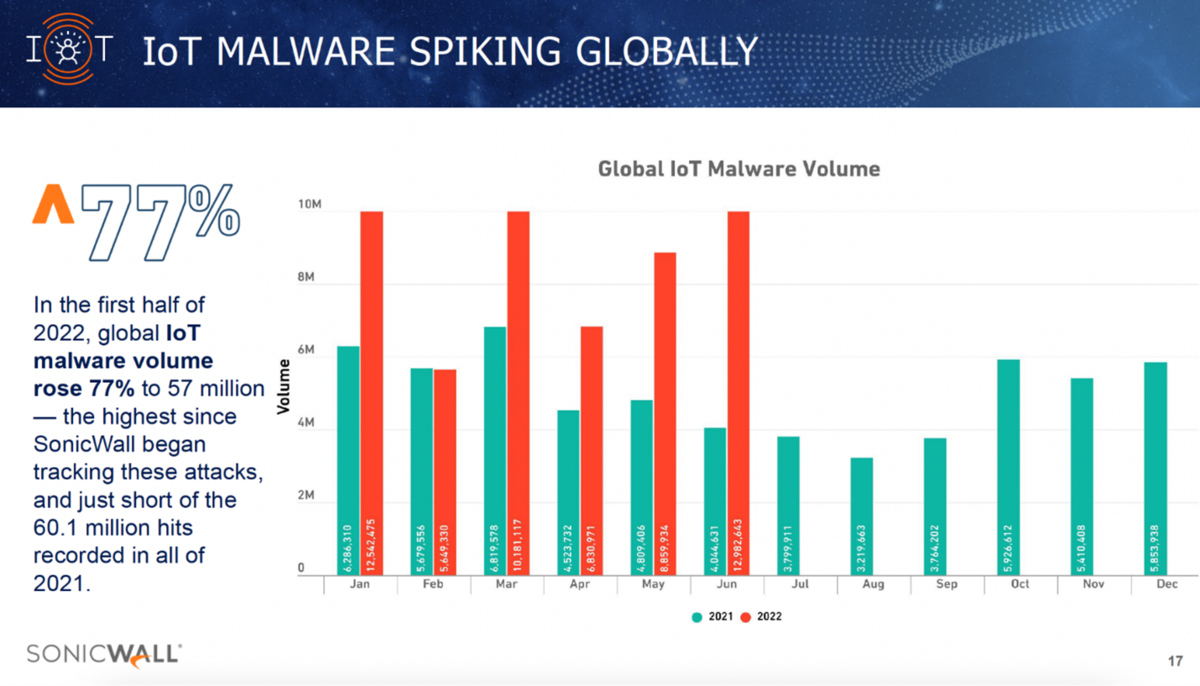
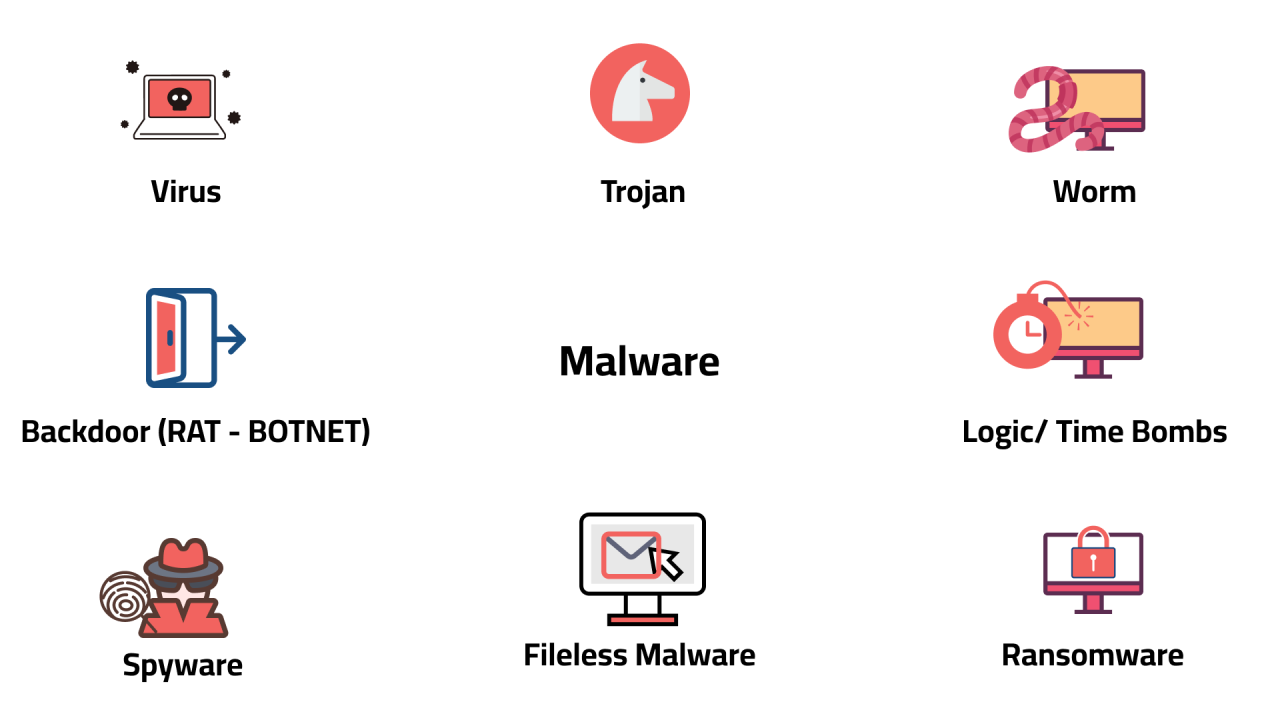
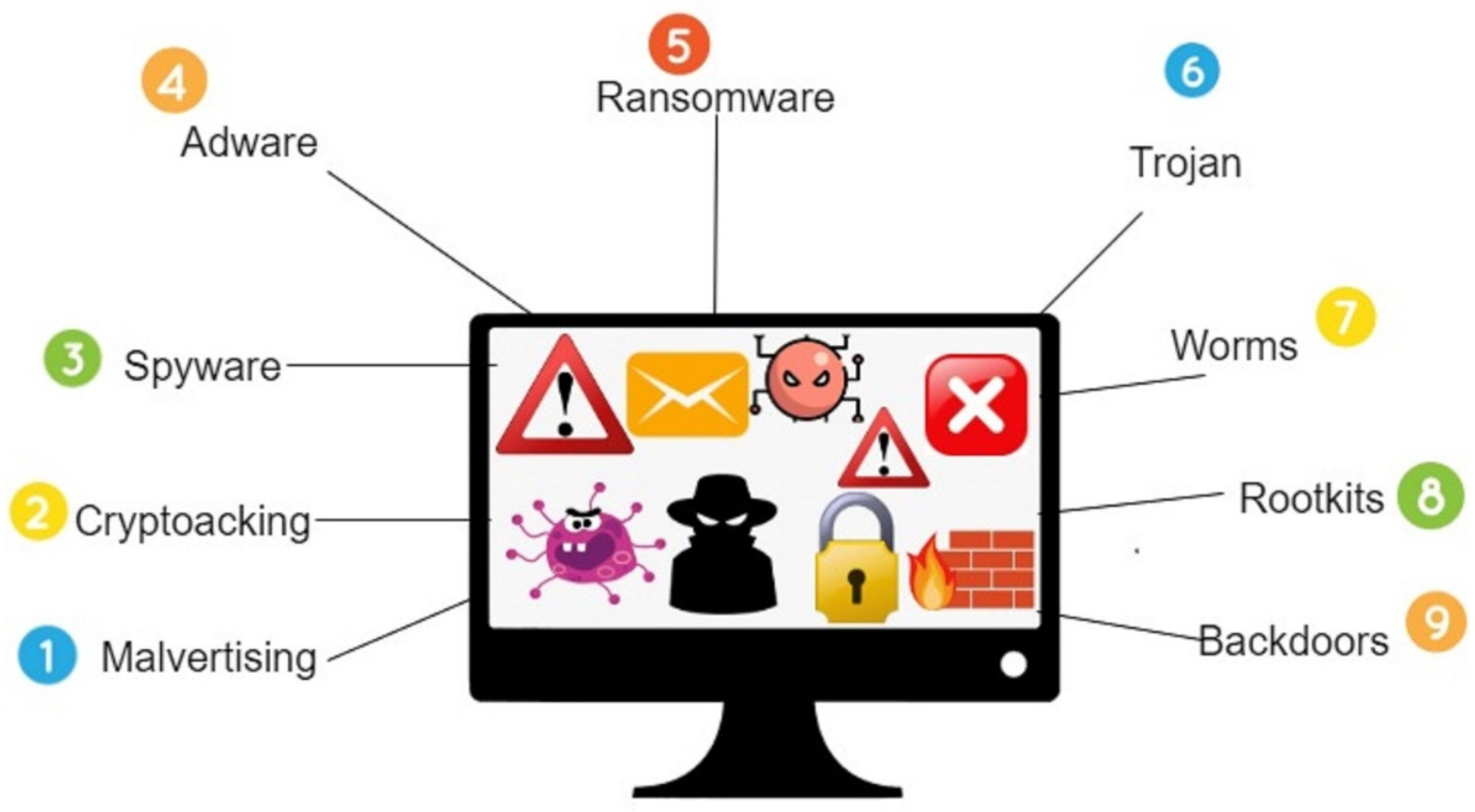
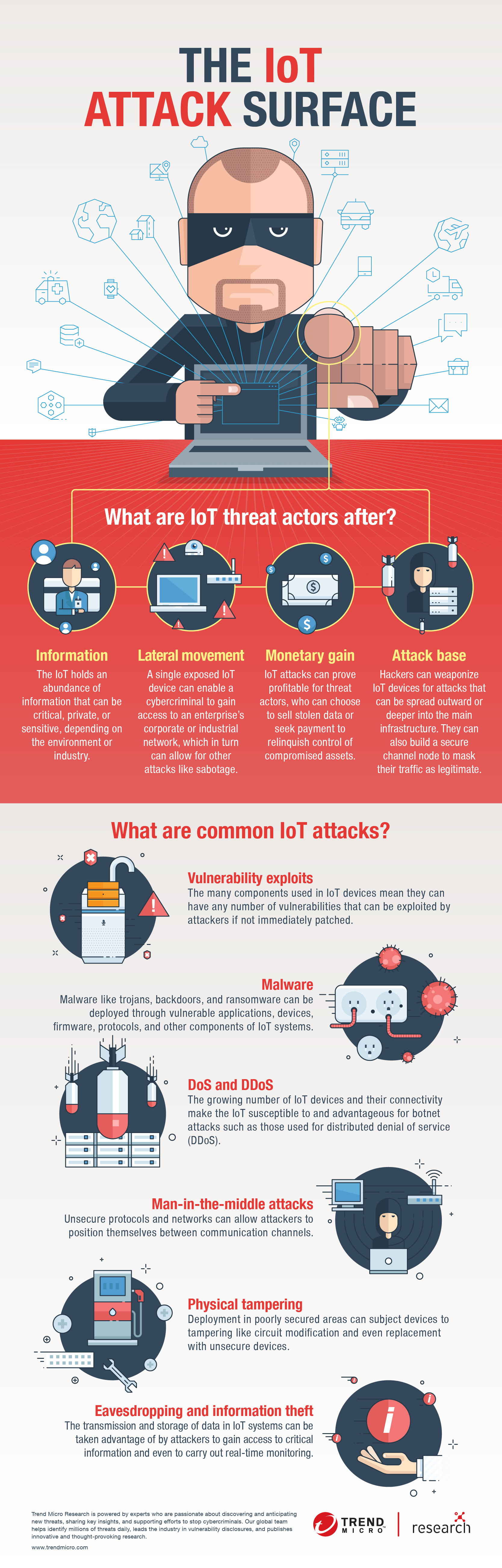
The Internet of Things (IoT) has revolutionized the way we live and work, with billions of connected devices transforming our homes, businesses, and industries. However, this increased connectivity has also created new vulnerabilities, making IoT devices a prime target for malware and cyber attacks. In this article, we will explore the risks associated with IoT malware and provide actionable tips on how to protect against these threats.Understanding IoT Malware
Protecting against IoT Malware
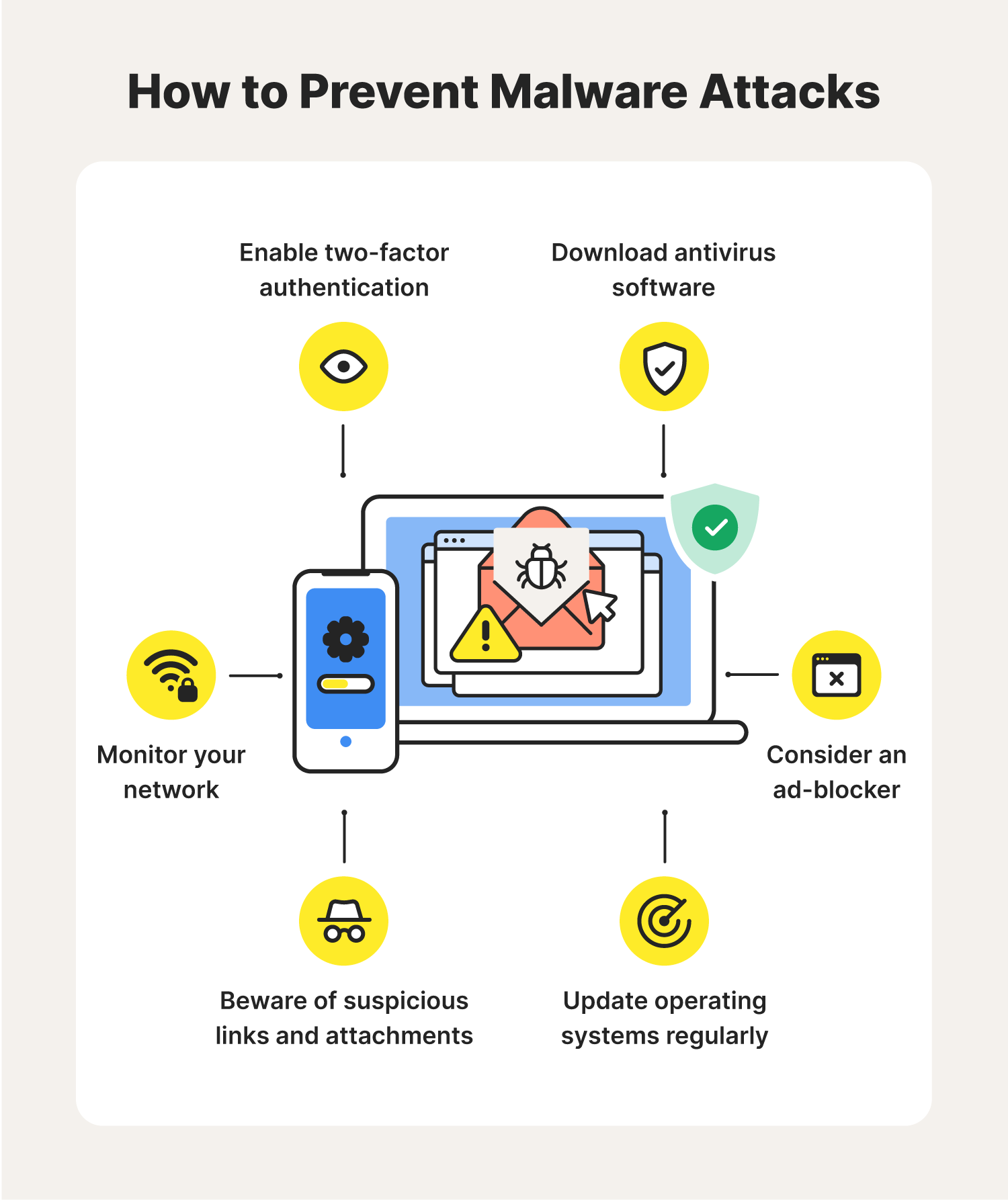
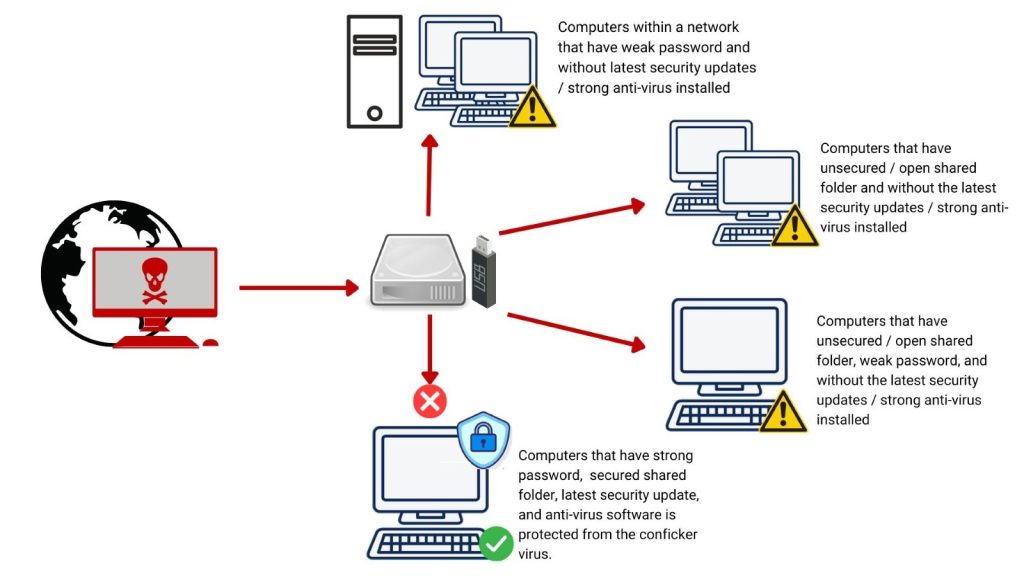
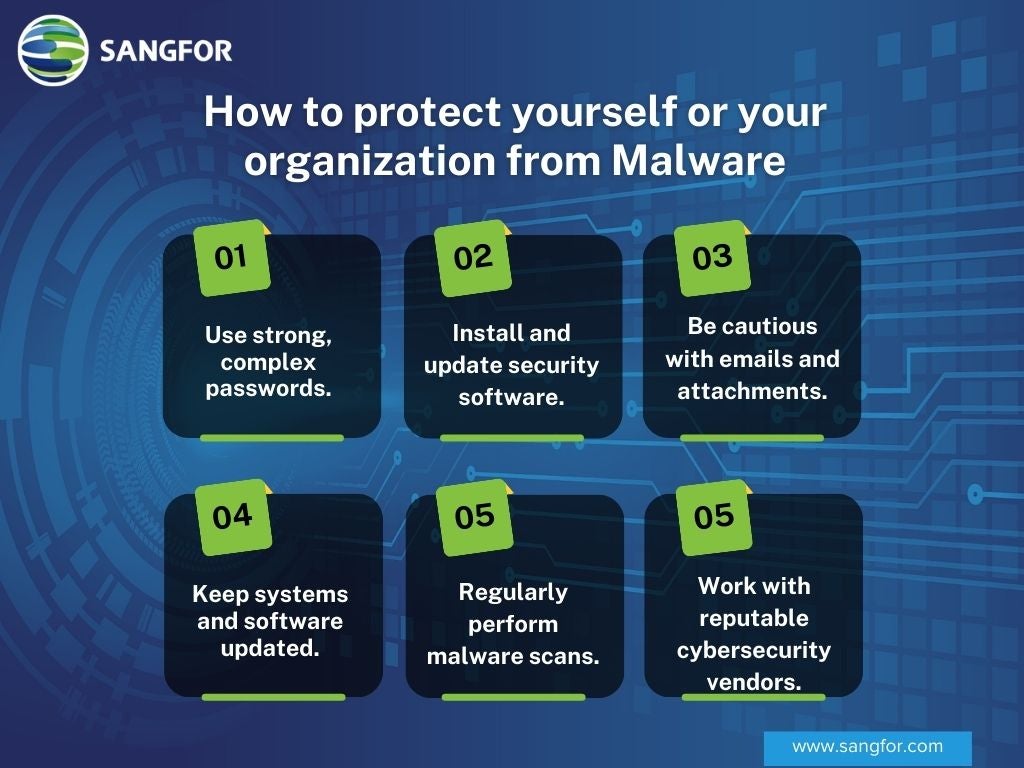
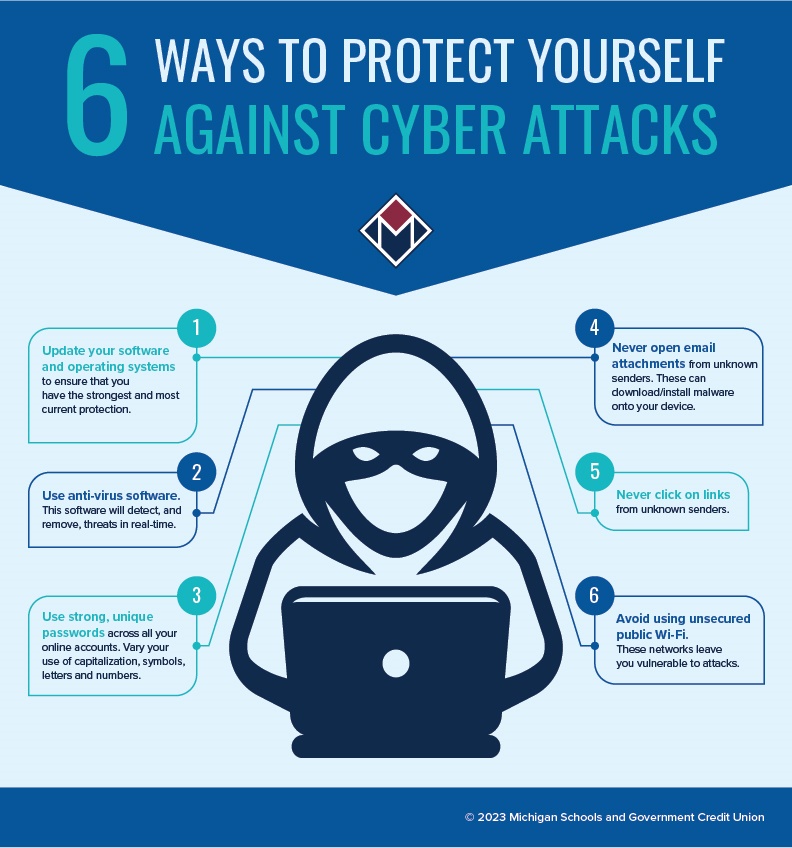
Protecting IoT devices from malware requires a multi-faceted approach that involves: * **Implementing secure design and development practices**: Ensure that IoT devices are designed with security in mind from the outset, with robust security protocols and mechanisms in place. * **Enforcing strong authentication and authorization**: Use multi-factor authentication, encryption, and secure key management to protect IoT devices and data. * **Monitoring and analyzing IoT traffic and events**: Implement intrusion detection and prevention systems to monitor and analyze IoT traffic and events in real-time. * **Regularly updating and patching IoT devices**: Keep IoT devices up-to-date with the latest security patches and firmware updates. * **Implementing network segmentation**: Segment IoT devices and networks to prevent lateral movement and contain potential threats.Best Practices for IoT Security

This particular example perfectly highlights why Protecting Against Malware On Iot Devices is so captivating.
In addition to the above measures, consider the following best practices for IoT security: * **Use antivirus software**: Install and regularly update antivirus software on IoT devices to detect and prevent malware attacks. * **Use secure communication protocols**: Use secure communication protocols, such as TLS and HTTPS, to protect IoT device communications. * **Implement device-level security**: Implement device-level security measures, such as secure boot processes and firmware integrity checks, to prevent malware infections. * **Monitor IoT device activity**: Regularly monitor IoT device activity to detect and respond to potential security incidents. * **Establish incident response plans**: Establish incident response plans to quickly respond to and contain IoT-related security incidents.