Single-Factor User Authentication Best Practices: A Comprehensive Guide
What is Single-Factor User Authentication?
Single-factor user authentication requires only one form of verification, such as a username and password, a PIN, or a fingerprint. This method of authentication has its limitations, as it can be easily compromised by phishing, credential stuffing, or other types of social engineering attacks.
Single-Factor User Authentication Challenges
The main challenge with single-factor user authentication is its vulnerability to attacks. Here are some of the key challenges:
This particular example perfectly highlights why Single-Factor User Authentication Best Practices is so captivating.
- Phishing and social engineering attacks
- Credential stuffing and brute-force attacks
- Weak passwords and poor password management
- Outdated and insecure authentication protocols
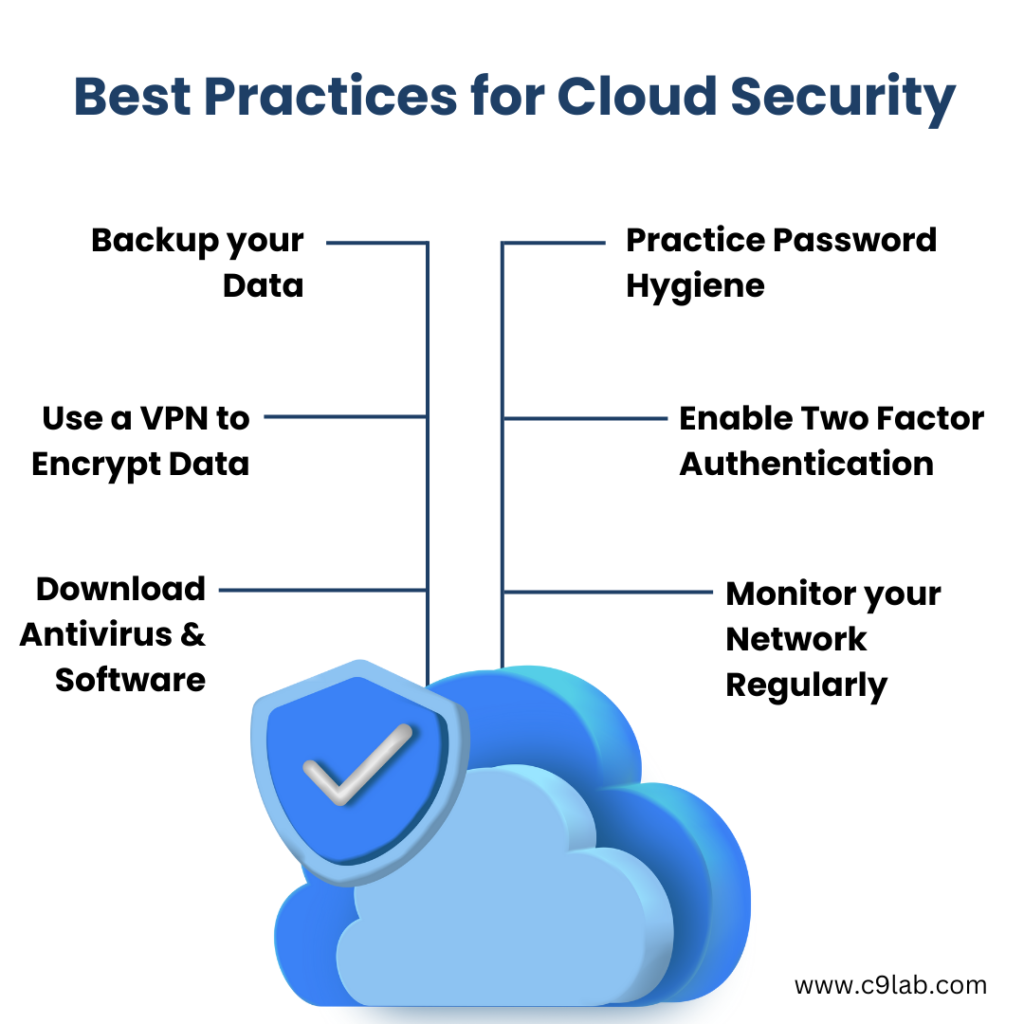
Best Practices for Single-Factor User Authentication
To mitigate the risks associated with single-factor user authentication, follow these best practices:
- Implement strong passwords and password policies: Enforce password rotation, require strong password complexity, and use password strengthening tools.
- Use secure protocols**: Implement secure protocols such as SAML, OAuth 2.0, OpenID Connect, or FIDO2, which provide an additional layer of security.
- Limit login attempts**: Implement CAPTCHAs or honeypot traps to prevent brute-force attacks.
- Monitor login activity**: Track login attempts, failed attempts, and suspicious activity to detect potential security breaches.
- Regularly update and patch authentication systems**: Ensure that authentication systems and protocols are up-to-date and patched to prevent exploitation of known vulnerabilities.

Moving forward, it's essential to keep these visual contexts in mind when discussing Single-Factor User Authentication Best Practices.
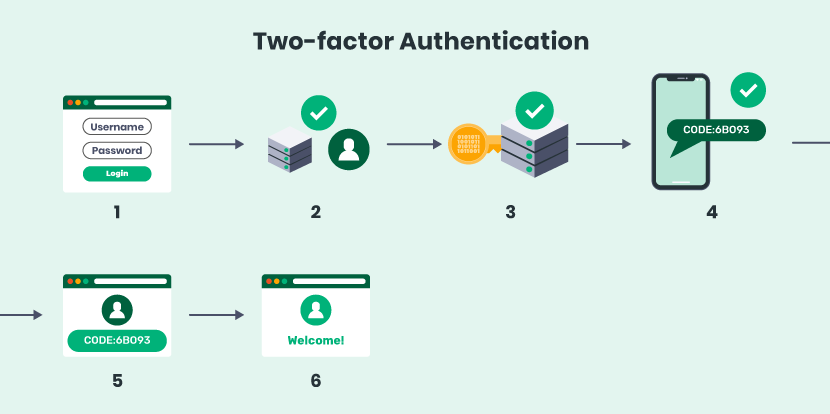
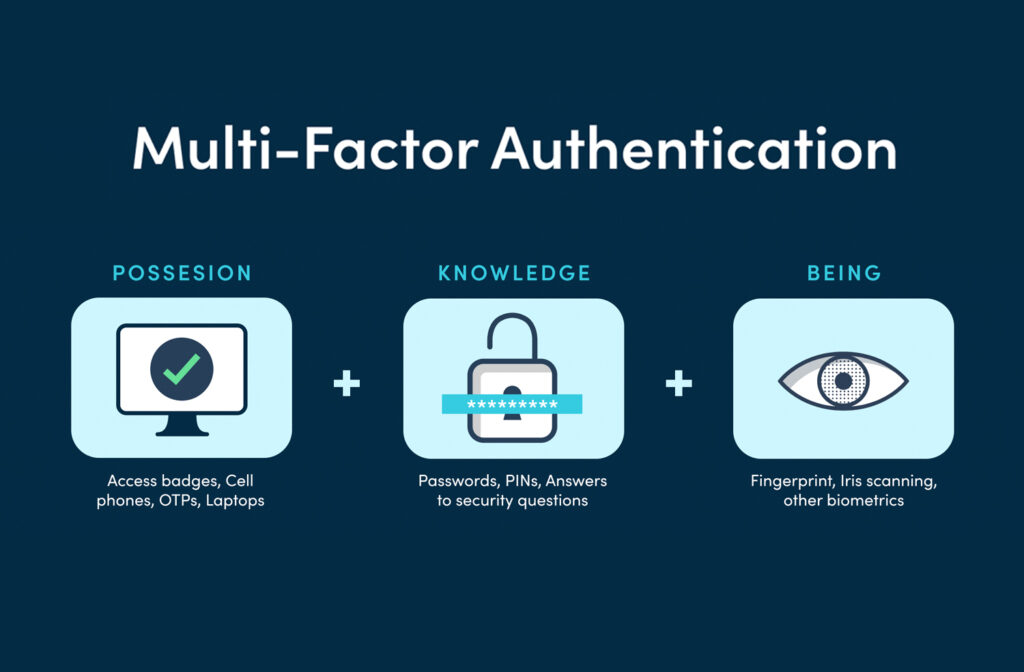
Alternatives to Single-Factor User Authentication
Single-factor user authentication is no longer considered a secure method for authentication. To strengthen your security posture, consider alternatives like:
Conclusion
In conclusion, single-factor user authentication is no longer a secure method for authentication. To protect your systems, applications, and data, implement the best practices mentioned above, and consider using alternatives like multi-factor authentication, passive authentication, or security keys. By doing so, you will reduce the risk of breaches and strengthen your security posture.