Wireless G Network Security Setup for Large Businesses: A Comprehensive Guide
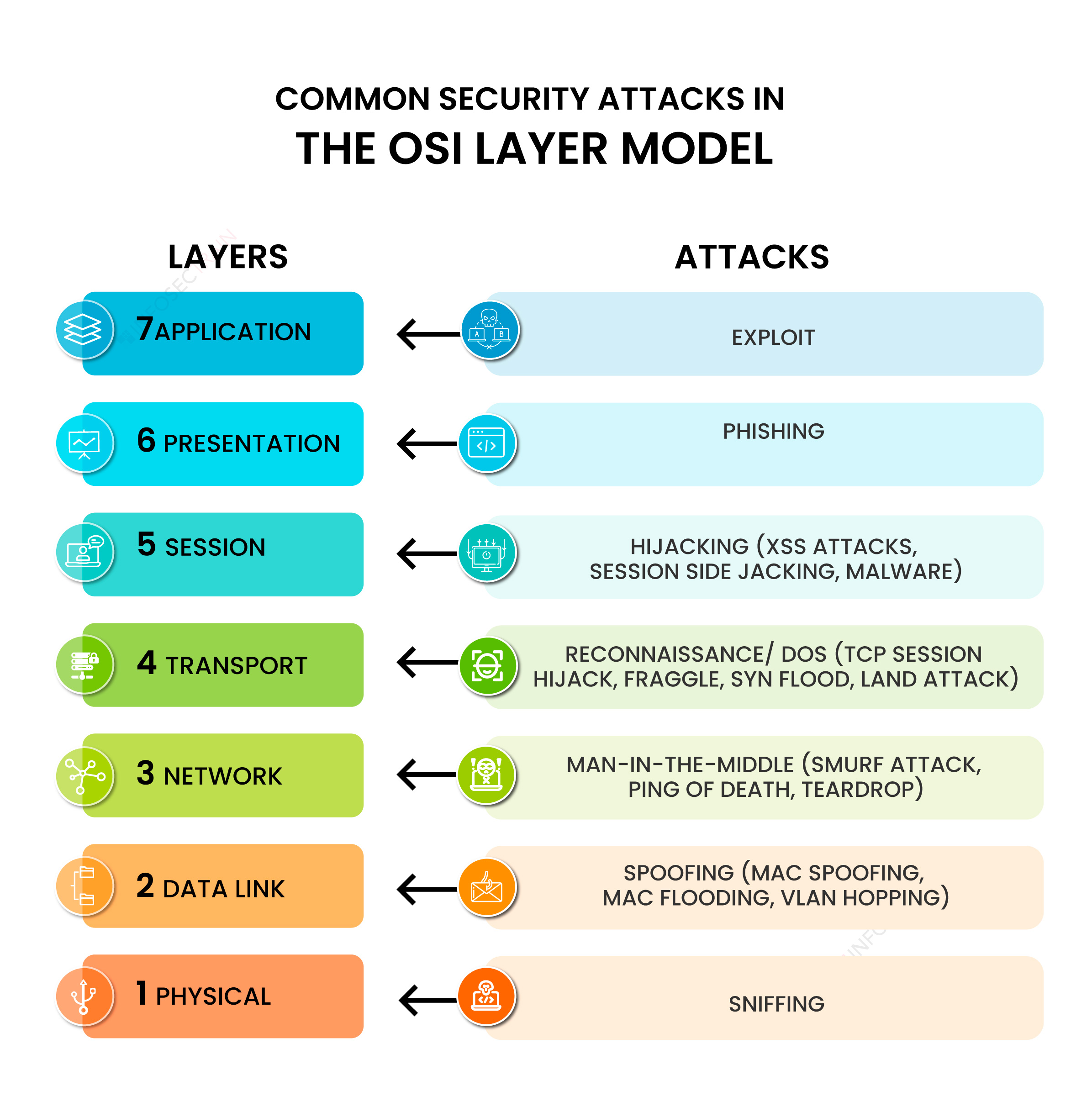
In today's digital landscape, wireless networks have become a crucial part of any large business's infrastructure. However, with the rise of wireless networks comes the risks of cyber threats and data breaches. In this article, we will delve into the world of Wireless G network security setup for large businesses, providing you with a comprehensive guide to securing your wireless network and protecting your sensitive data.
What is Wireless G Network Security?
Why is Wireless G Network Security Important for Large Businesses?
- Protects sensitive business data from unauthorized access
- Prevents hacking and cyber attacks
- Ensures network reliability and availability
- Complies with industry regulations and standards
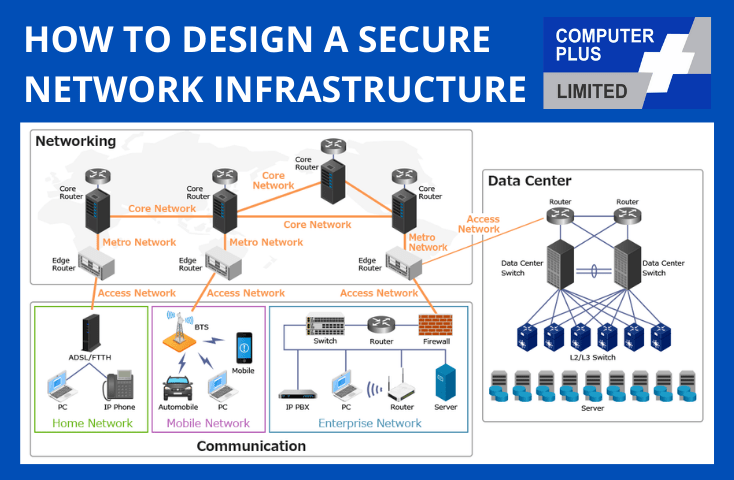
Wireless G Network Security Setup for Large Businesses: Best Practices
Here are some best practices to consider when setting up a Wireless G network security setup for large businesses:

1. Use Strong Encryption
Use WPA3 as the encryption protocol, which is the most secure standard currently available. WPA3 provides robust encryption and authentication capabilities, ensuring that data transmitted over the wireless network is secure and private.
2. Set Up Access Control
Implement access control measures such as MAC address filtering, which allows only authorized devices to connect to the network. This ensures that unauthorized devices are not able to connect to the network and access sensitive business data.
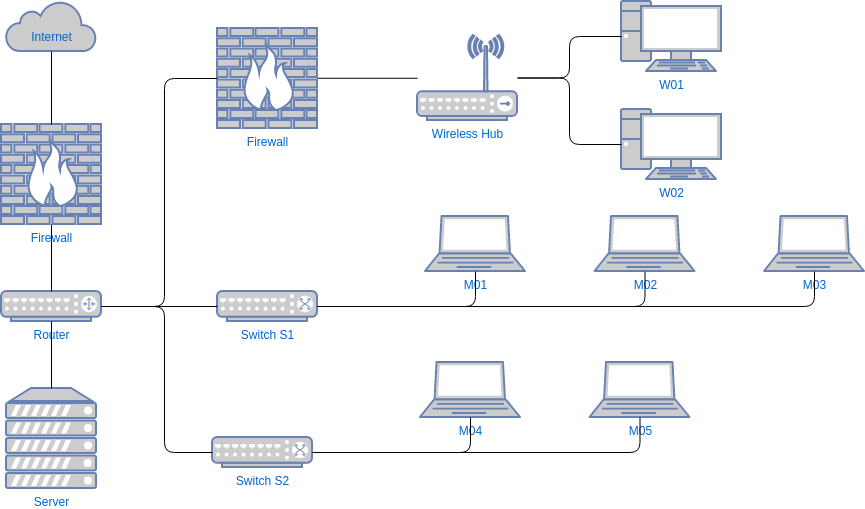
3. Use Firewall and Router
Use a firewall and router to control incoming and outgoing network traffic. This ensures that only authorized traffic is allowed to enter or exit the network, preventing hacking and cyber attacks.

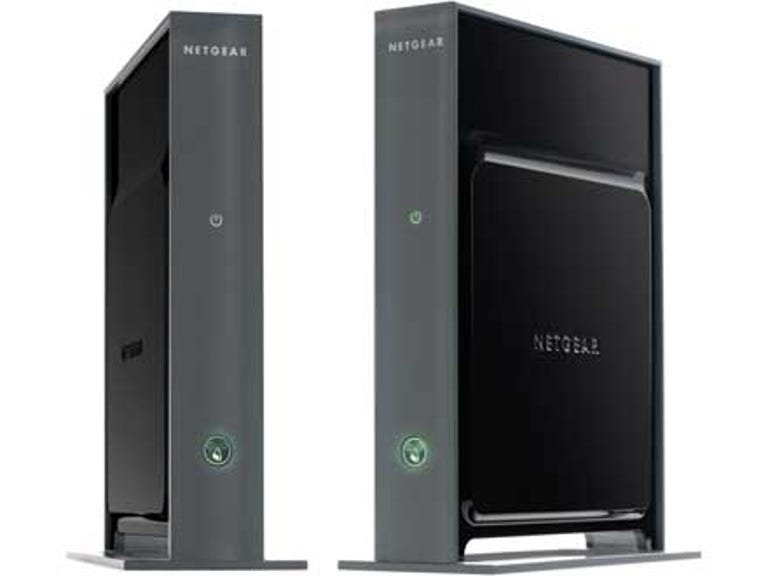
As we can see from the illustration, Wireless G Network Security Setup For Large Businesses has many fascinating aspects to explore.
4. Regularly Update and Patch Devices
Regularly update and patch devices such as laptops, smartphones, and tablets to ensure that they have the latest security patches and updates. This ensures that devices are secure and protected from known vulnerabilities.
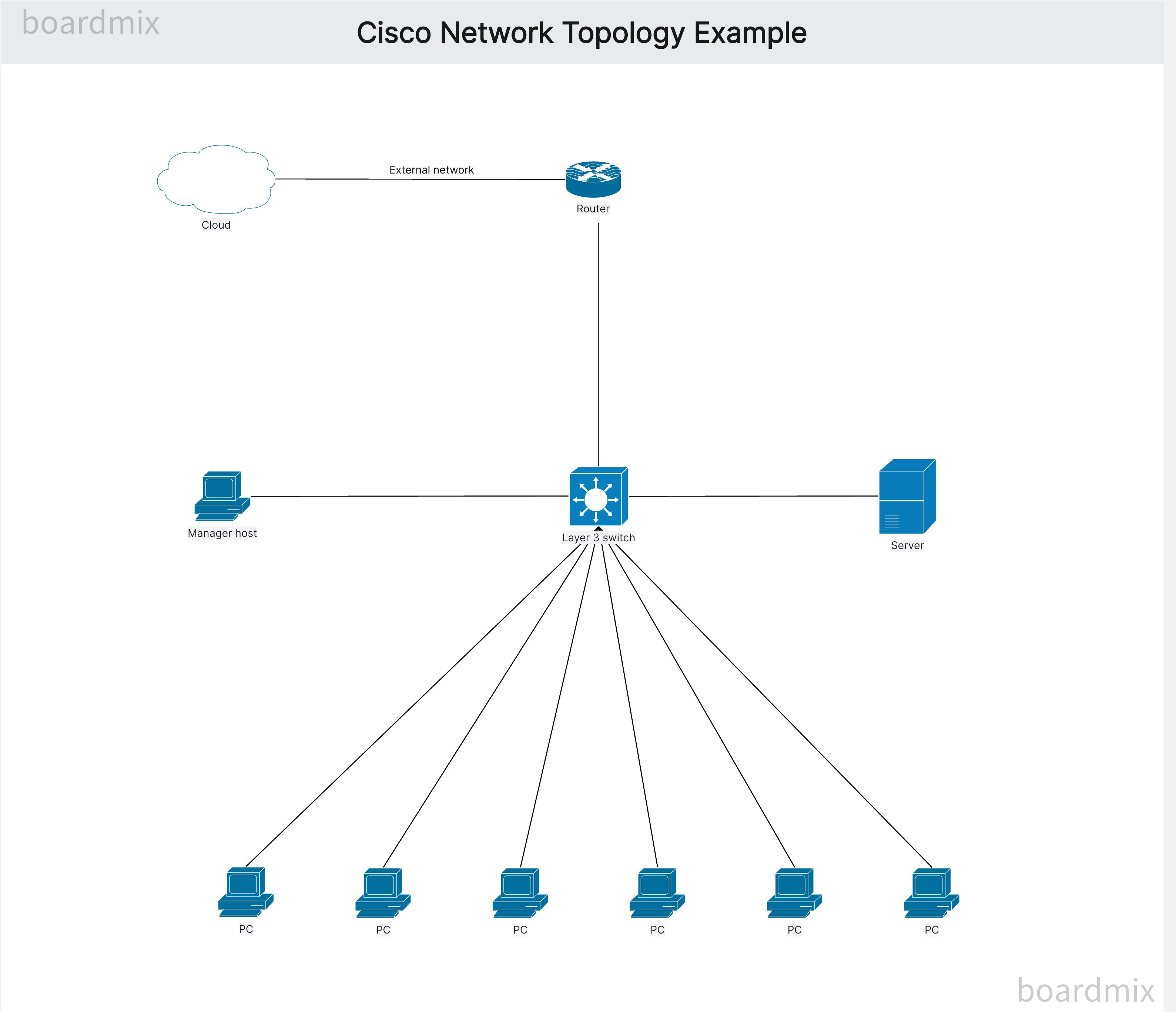
5. Use Network Segmentation
Use network segmentation to isolate sensitive data and applications from the rest of the network. This ensures that even if a device is compromised, it will not have access to sensitive business data.
Implement a SIEM system to monitor and analyze network traffic for potential security threats. This ensures that potential security threats are detected and responded to in a timely manner.
7. Conduct Regular Security Audits
Conduct regular security audits to identify and address potential security vulnerabilities. This ensures that the wireless network is secure and up-to-date with the latest security best practices.
Conclusion
Wireless G network security setup for large businesses is a critical component of any business infrastructure. By following the best practices outlined in this article, businesses can ensure that their wireless networks are secure, reliable, and protected from cyber threats. Remember, security is an ongoing process, and businesses should regularly review and update their security measures to ensure that they remain secure and up-to-date with the latest security best practices.
References
AST Networks, "Setup a Secure Wireless Network for Your Business," March 11, 2026. Business Insider, "T-Mobile's Wireless Solutions for All Businesses," Accessed March 10, 2026. Light Reading, "How to Implement Wireless Network Security into Enterprise Wi-Fi Design," January 20, 2026. Verizon Business, "Setup a Reliable Small Business Wireless Network with Verizon," Accessed March 10, 2026. CIO.com, "7 Key Factors to Consider When Setting Up a Business Wi-Fi Network," March 13, 2025. Mitel, "Hybrid Business Communication Solutions," Accessed March 10, 2026. Motorola, "#hellomoto | Discover our new unlocked Android phones," Accessed March 10, 2026. Business Wi-Fi Security, "Essential Best Practices to Build a Reliable, High-Performing Wi-Fi Network," October 2, 2025. Wired, "How to Secure Your Wireless Network," May 1, 2025.






6.0-B_large_1578293078120u.jpg)




.png)





_4.0-310X223X70-L-7022506003_large_1614648496045z.jpg)
